前言
自 2024 年 6 月起,国内的 Docker 镜像陆续停止服务,这让本就困难的 Docker 使用环境更加雪上加霜。本文来配置一套包含 Docker、K8s、Quay、Ghcr、Mcr、elastic、nvcr 等镜像的本地加速服务,提升本地的容器使用体验。
为什么不在公网上部署呢,第一点面临的就是合规风险,部署在本地仅供内网使用可以规避掉很大一部分此类风险;其二就算不考虑合规问题国内的大带宽服务器价格高的吓人,有这样的成本倒不如去购买付费的商业化镜像方案来的便宜。
镜像项目介绍
本次我们使用的容器镜像项目加速地址为:
GitHub - dqzboy/Docker-Proxy: 🔥 🔥 🔥 自建Docker镜像加速服务,基于官方Docker Registry 一键部署Docker、K8s、Quay、Ghcr、Mcr、Nvcr等镜像加速\管理服务。支持免服务器部署到Render\Koyeb
项目特点:
- 一键部署 Docker 镜像代理服务的功能,支持基于官方 Docker Registry 的镜像代理
- 支持多个镜像仓库的代理,包括 Docker Hub、GitHub Container Registry(ghcr.io)、Quay Container Registry(quay.io)、Kubernetes Container Registry(k8s.gcr.io)、Microsoft Container(mcr.microsoft.com)、Elastic Stack(docker.elastic.co)
- 自动检查并安装所需的依赖软件,如 Docker\Compose、Nginx\Caddy 等,并确保系统环境满足运行要求
- 根据你所选择部署的 WEB 反代服务,自动渲染对应的 Nginx 或 Caddy 服务配置
- 自动清理注册表上传目录中的那些不再被任何镜像或清单引用的文件
- 支持自定义配置代理缓存时间 (PROXY_TTL)、支持配置 IP 黑白名单,防止恶意攻击行为
- 提供了服务管理、配置管理、服务卸载、认证授权等功能,方便用户进行日常管理和维护
- 支持一键配置本机 Docker 代理和容器服务代理 (HTTP_PROXY),仅支持 http
- 支持国内服务器一键部署,解决国内环境无法安装 Docker\Compose 服务难题
- 支持主流 Linux 发行版操作系统,例如 Centos、Ubuntu、Rocky、Debian、Rhel 等
- 支持主流 ARCH 架构下部署,包括 linux/amd64、linux/arm64
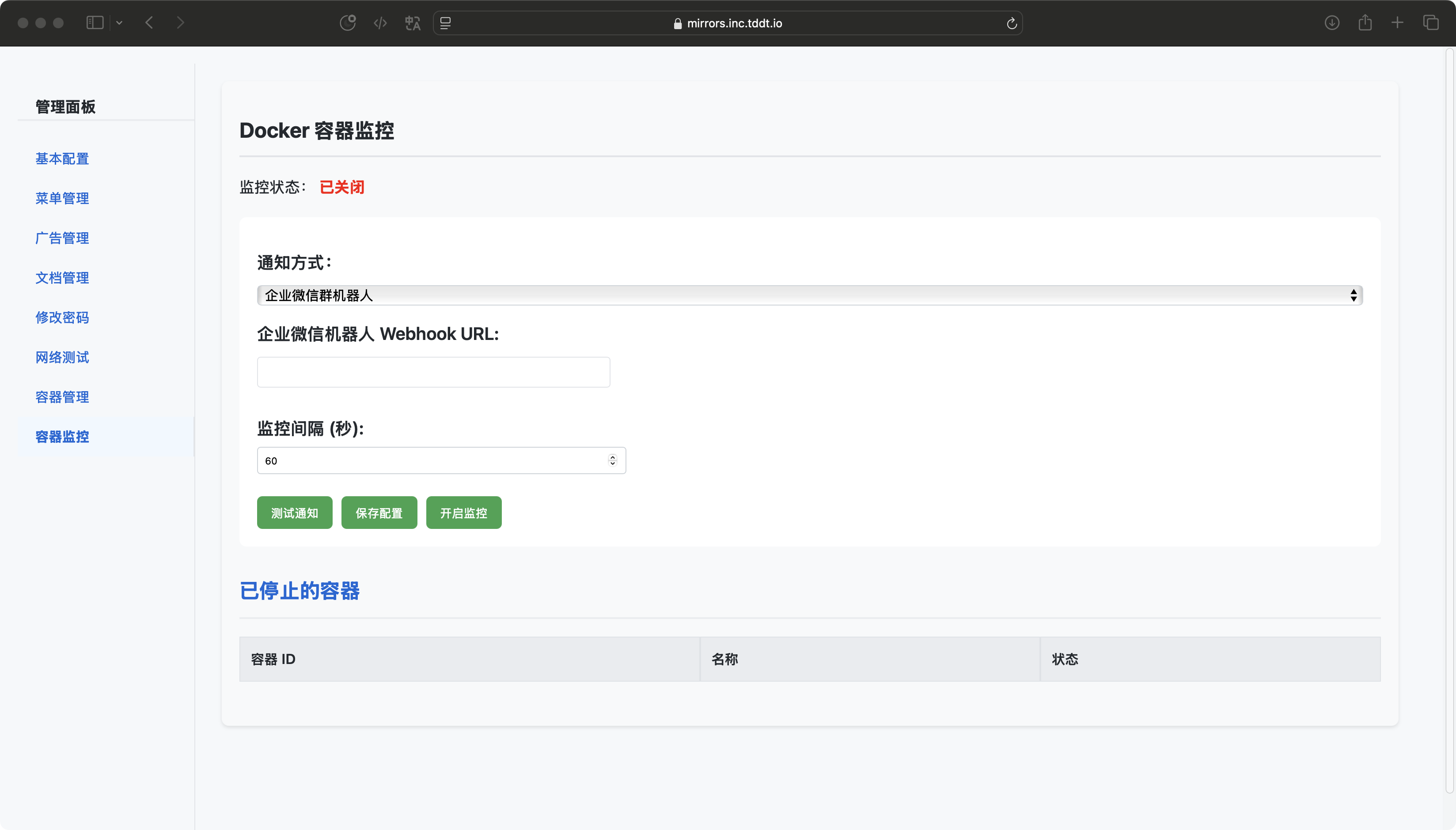
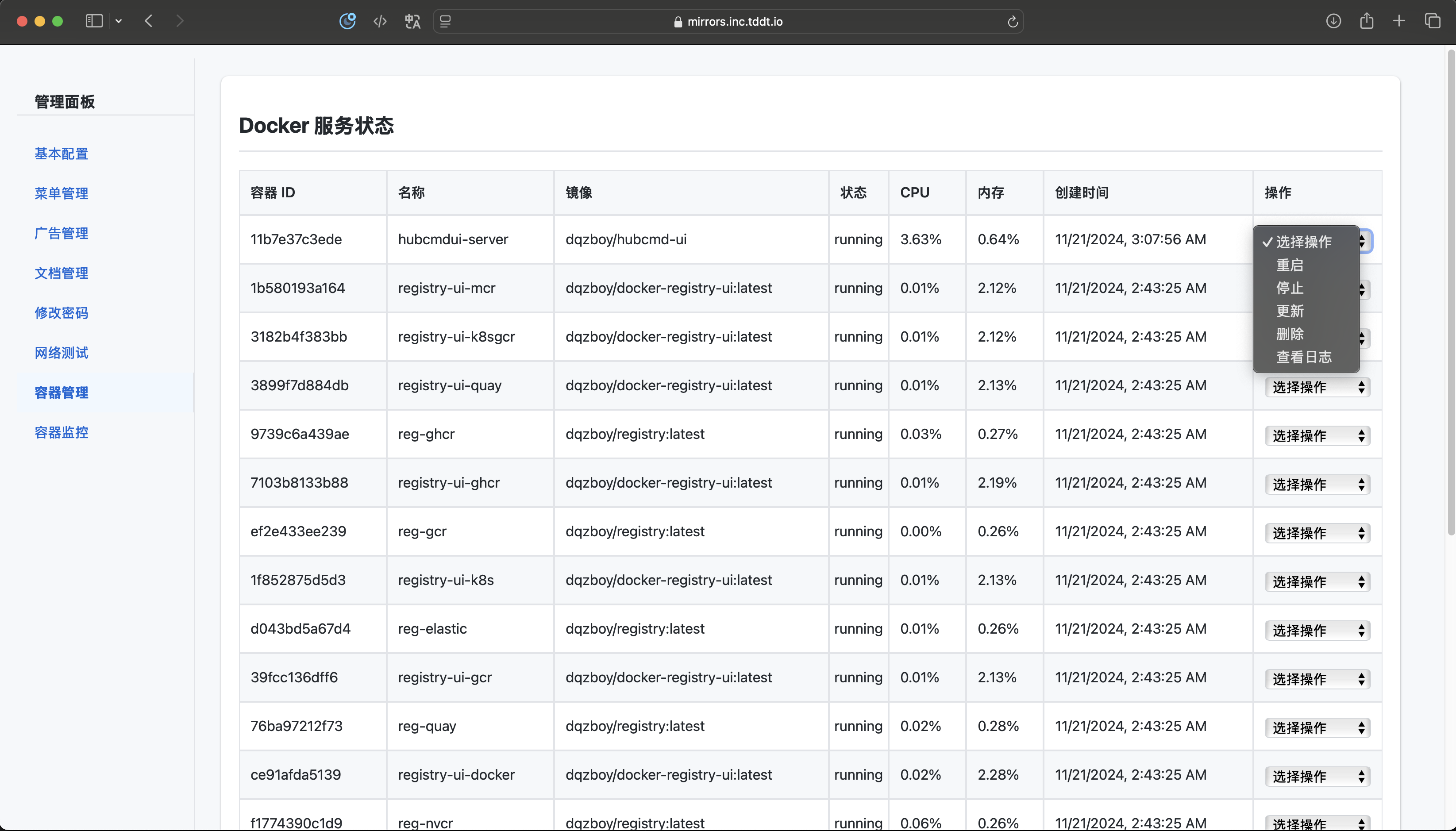
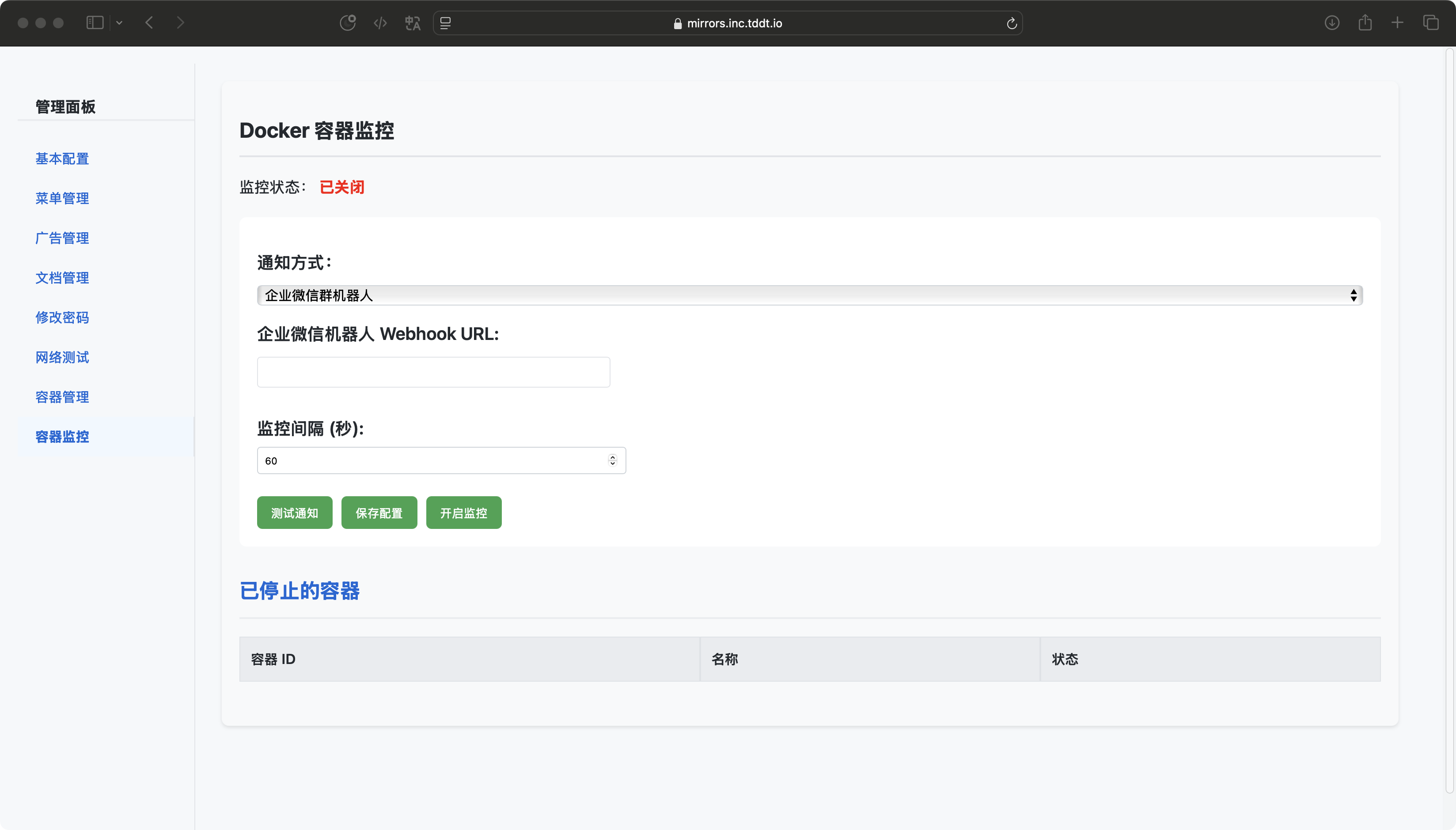
- 针对本项目开发 Docker Registry 管理面板,实现镜像搜索、广告展示、文档教程、容器管理、容器监控告警、网络测试等功能
开始部署
首先克隆项目:
1
| git clone https://github.com/dqzboy/Docker-Proxy.git
|

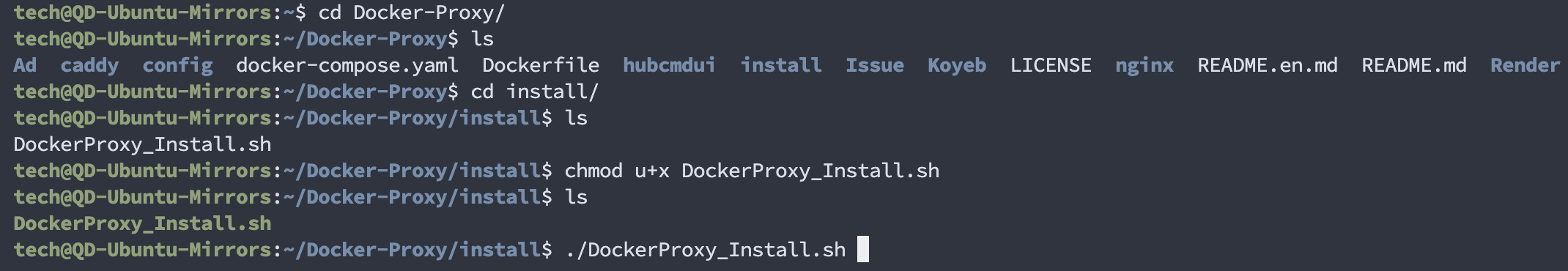
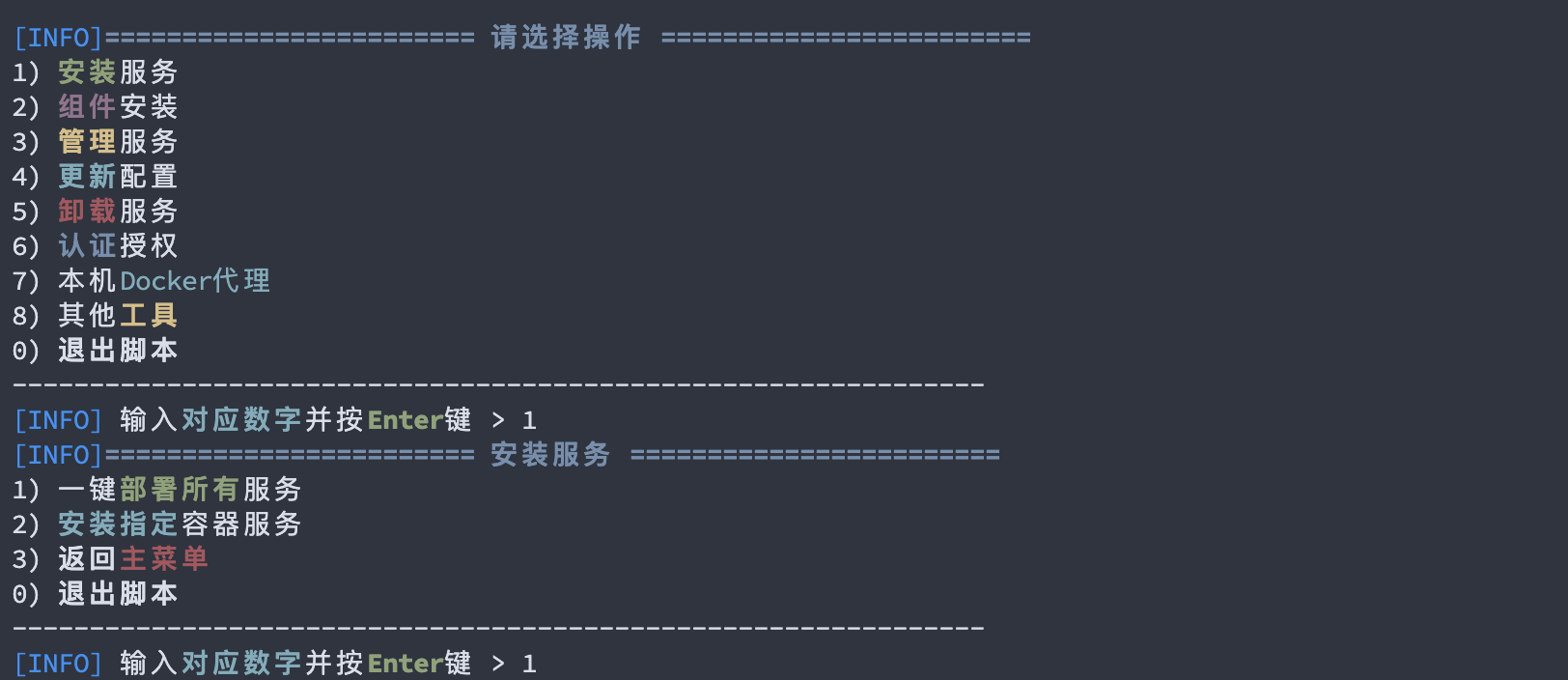
方法一:脚本安装
进入 install 目录,为安装脚本赋予执行权限并执行:
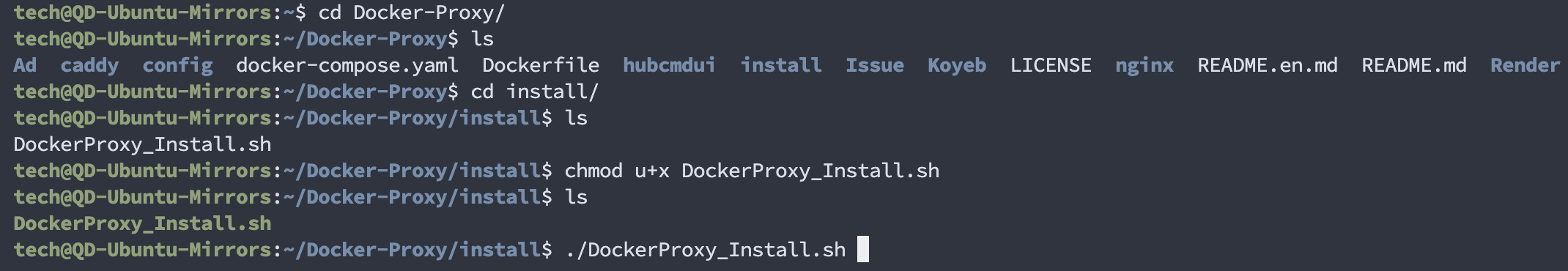
脚本需要 root 权限运行,这里加上 sudo:
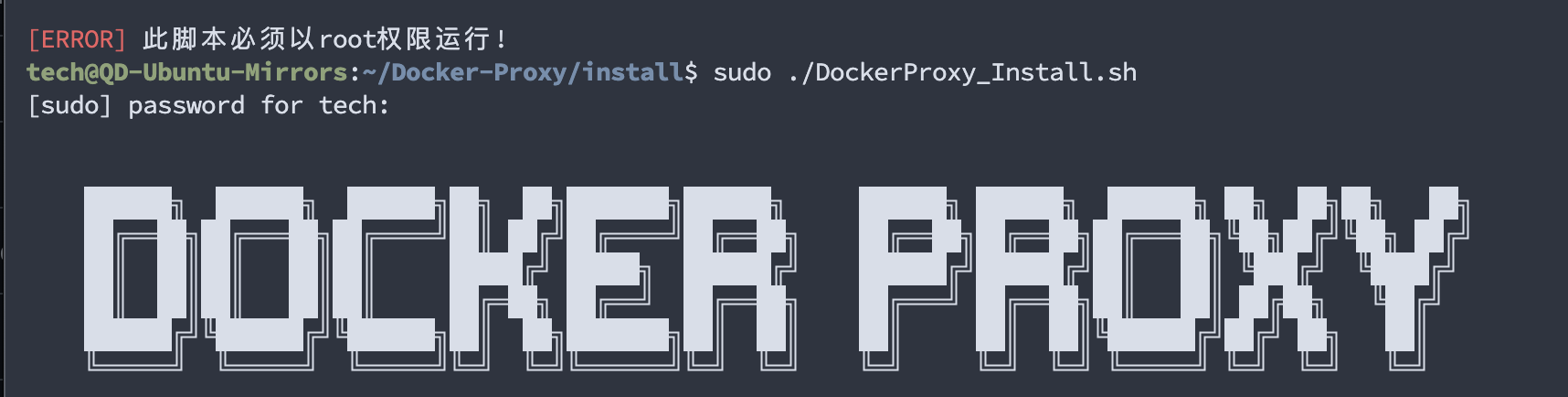
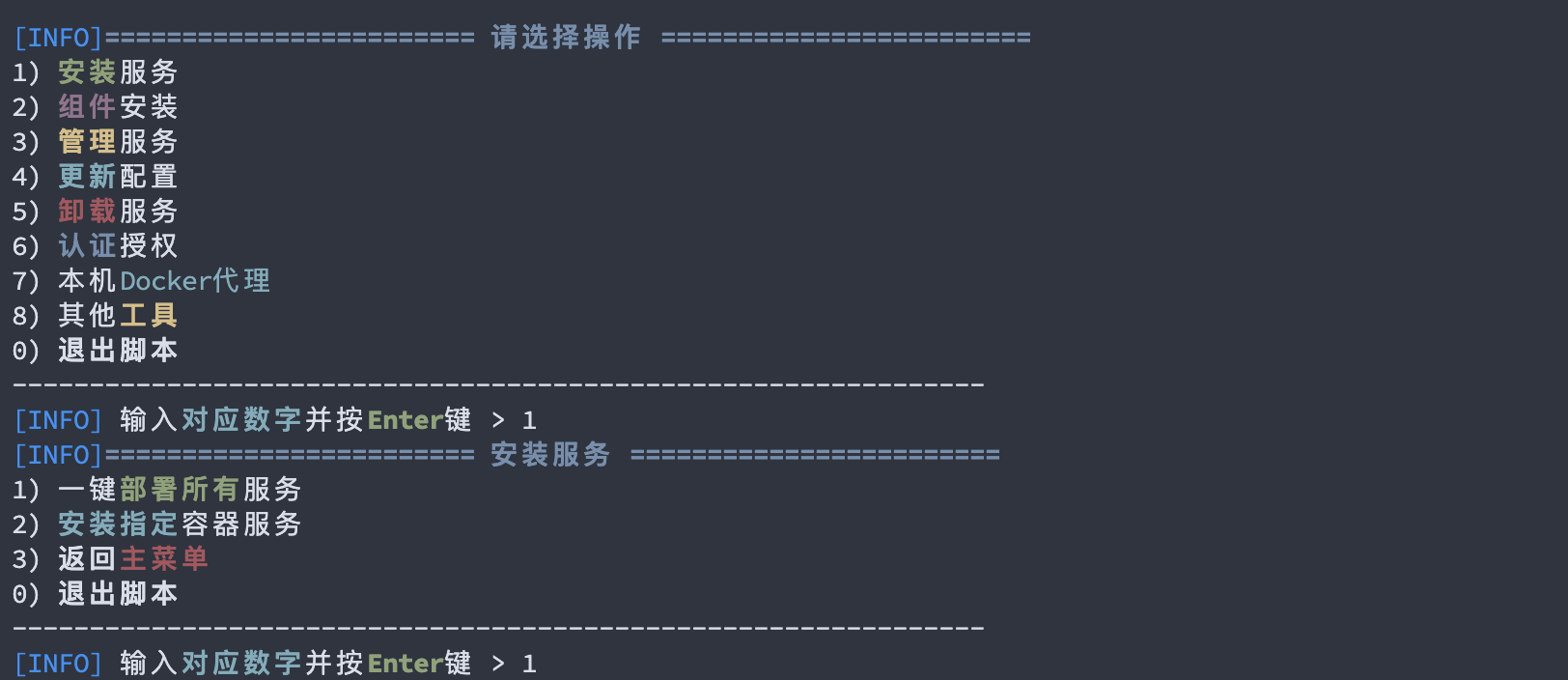
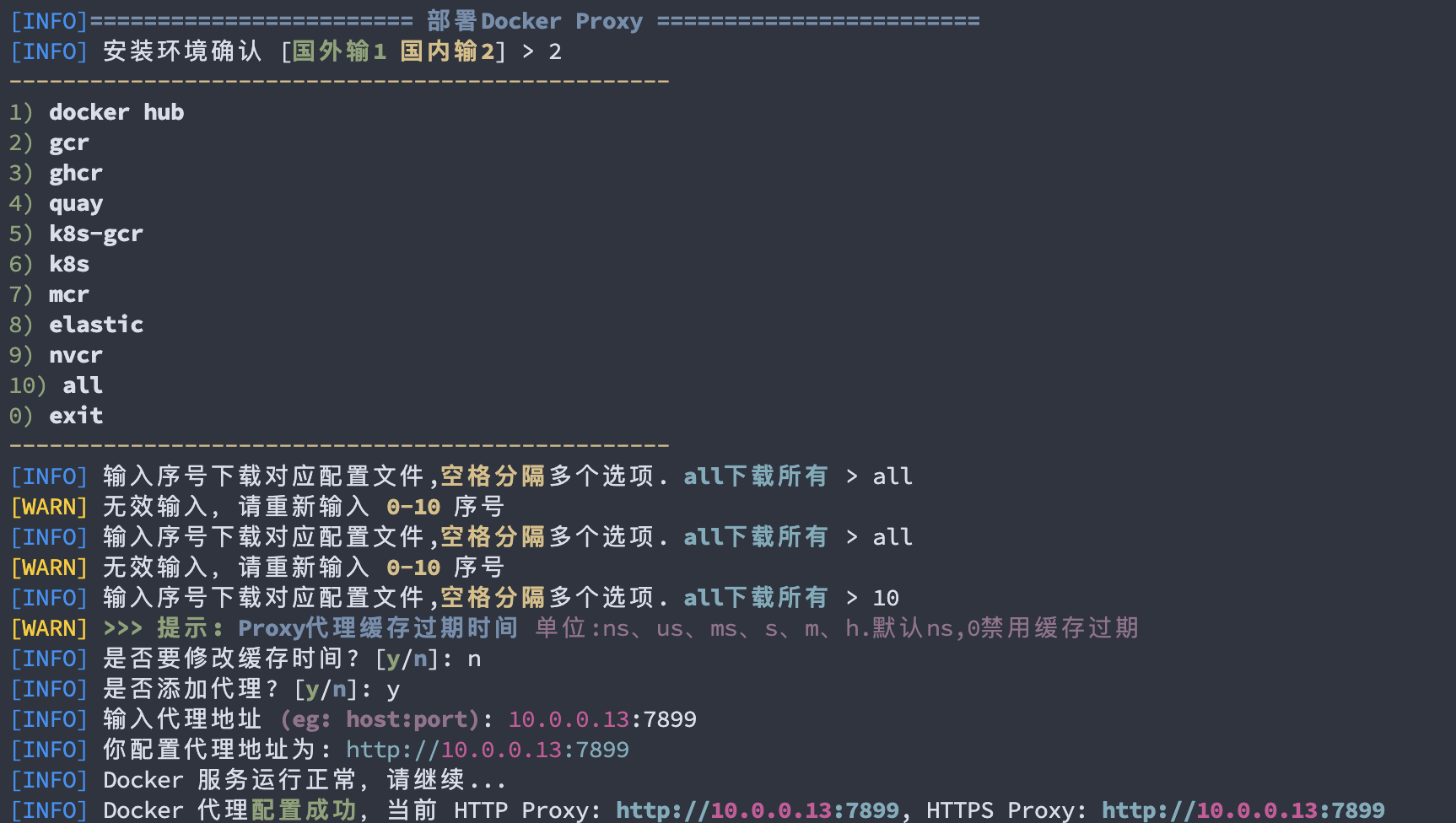
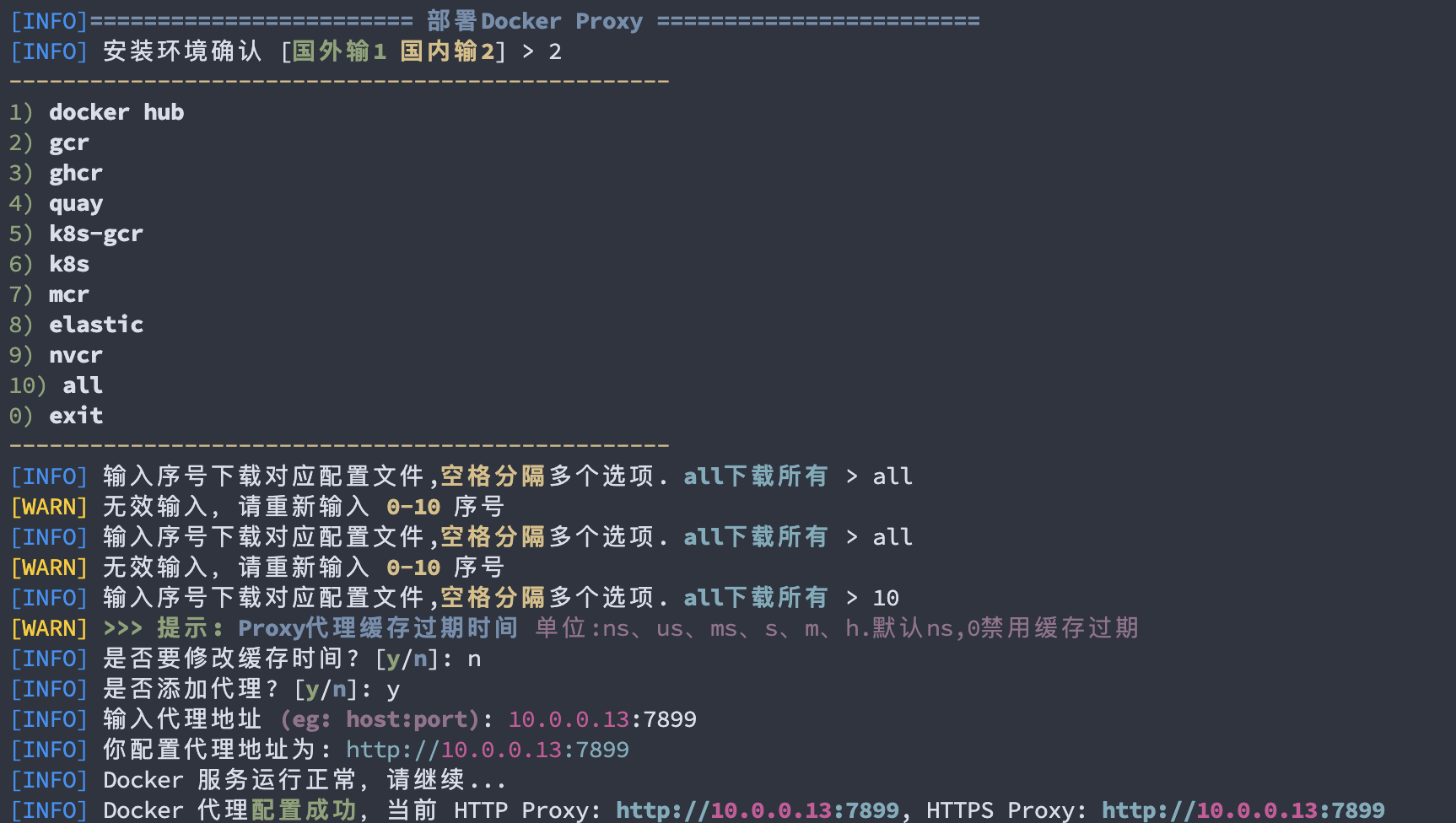
脚本安装比较简单,根据菜单提示进行选择即可:
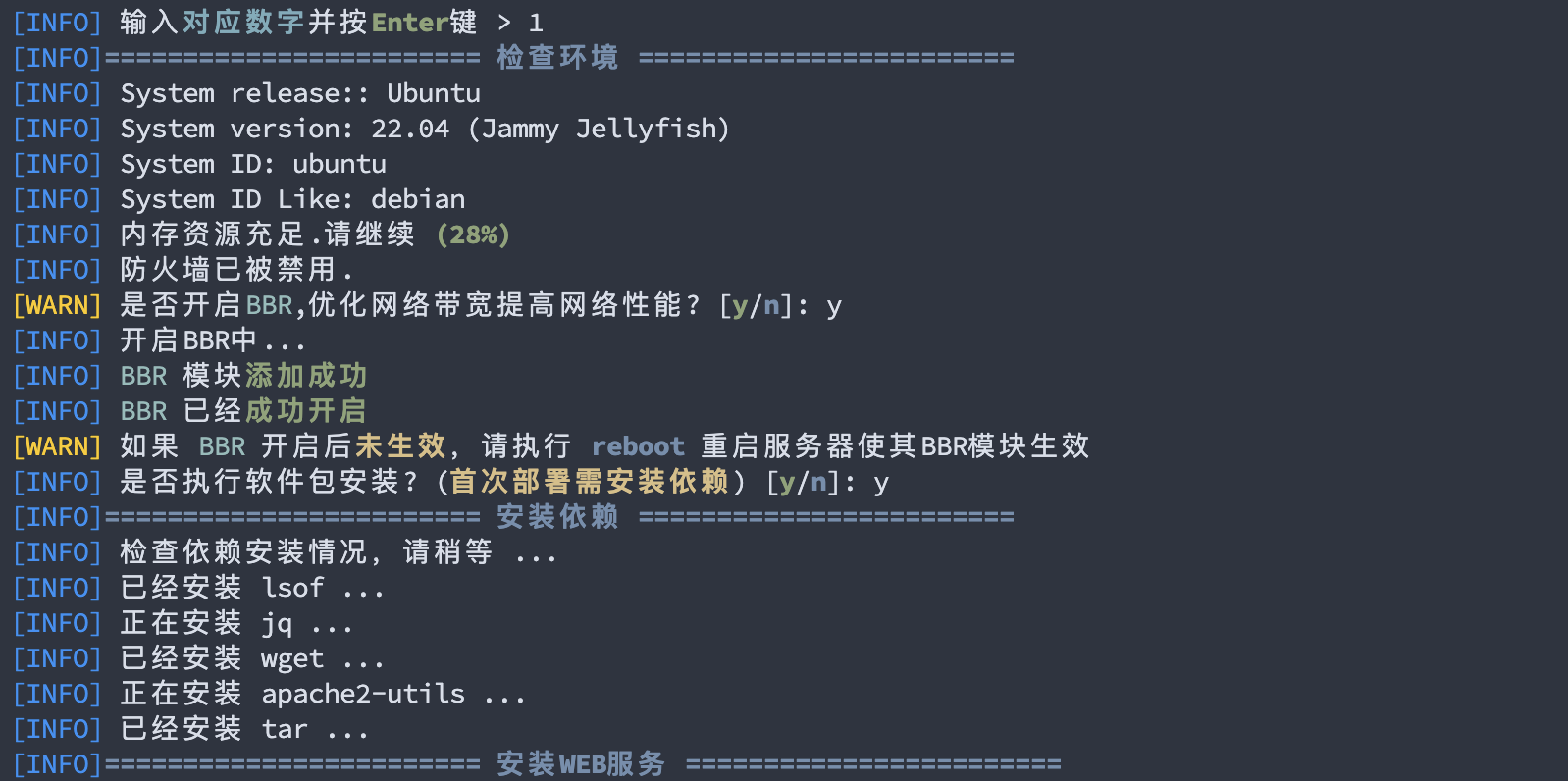
安装过程中会提示是否安装 Web 服务,由于我的服务器是已经有一个 Web 服务组件在运行了,再安装一定会端口冲突报错,我就先不安装了:

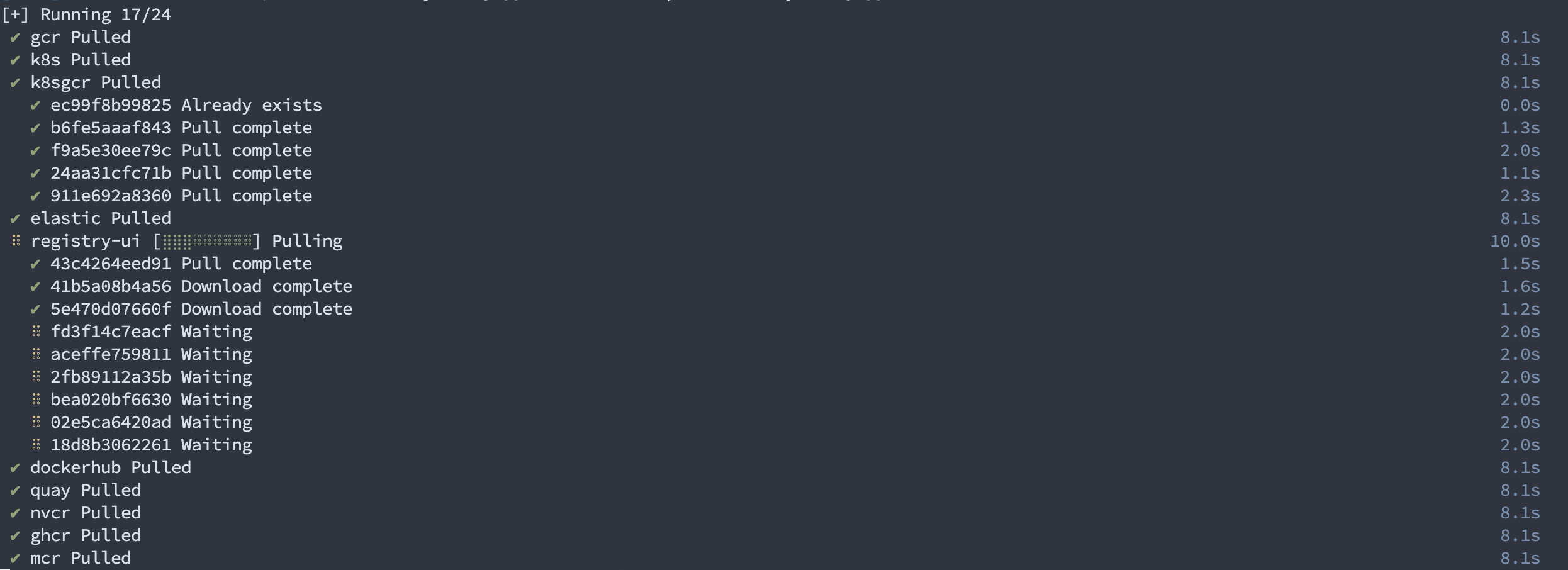
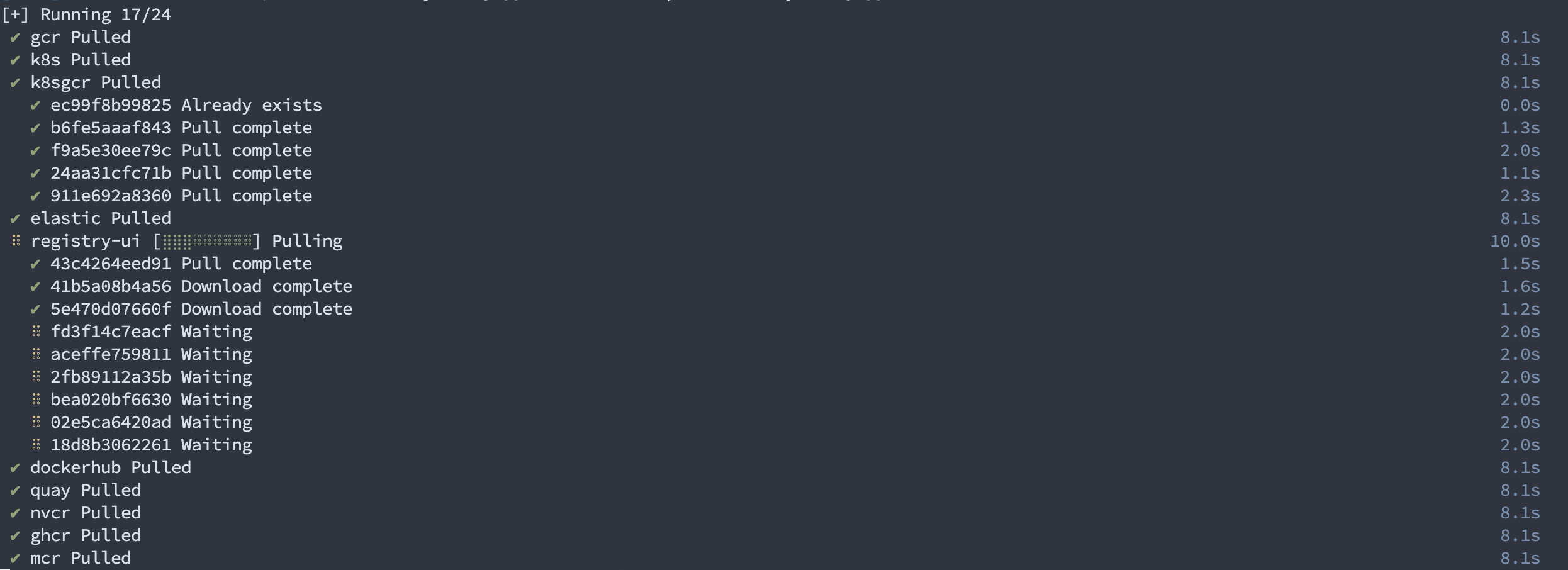
安装完成:

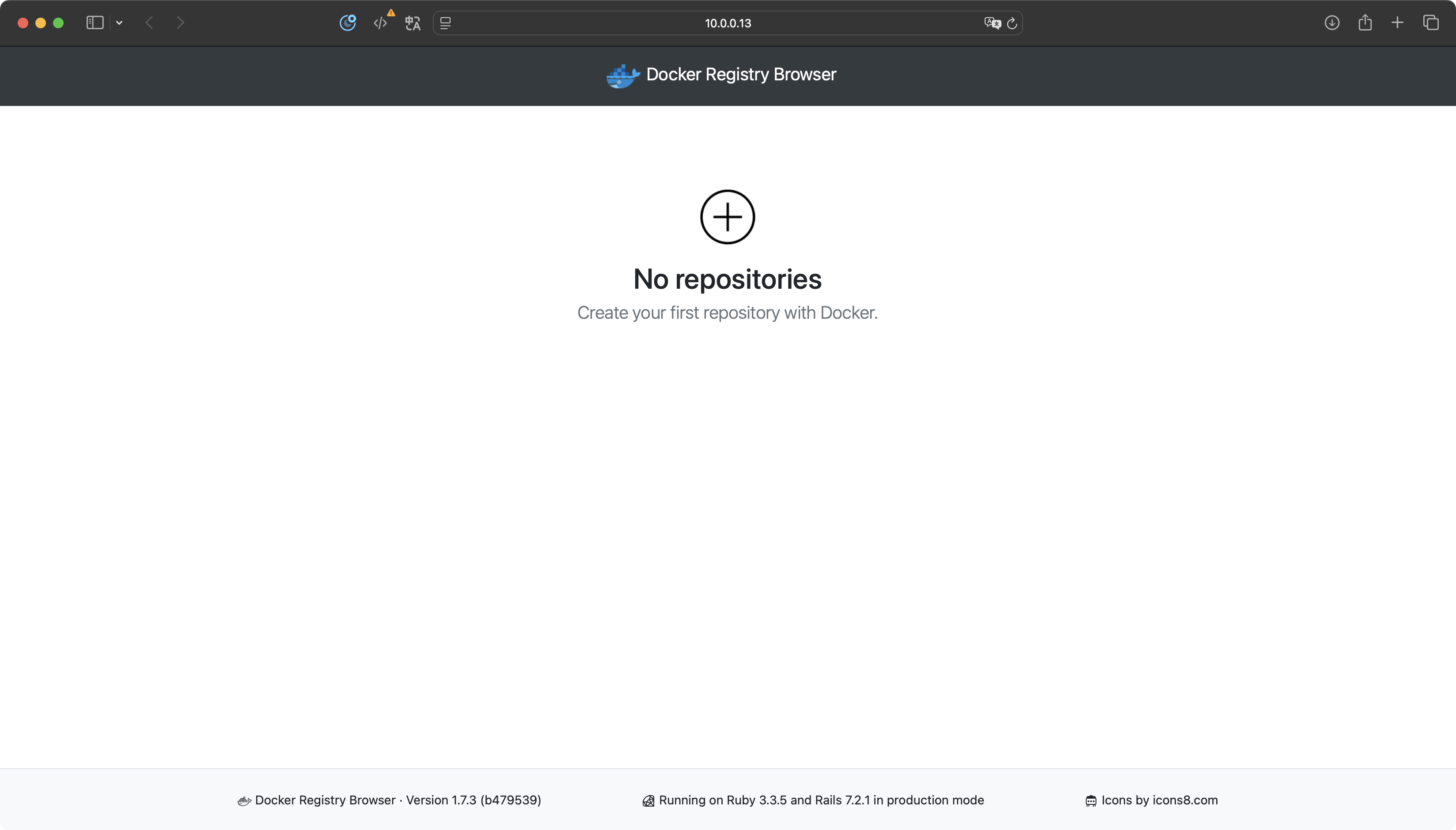
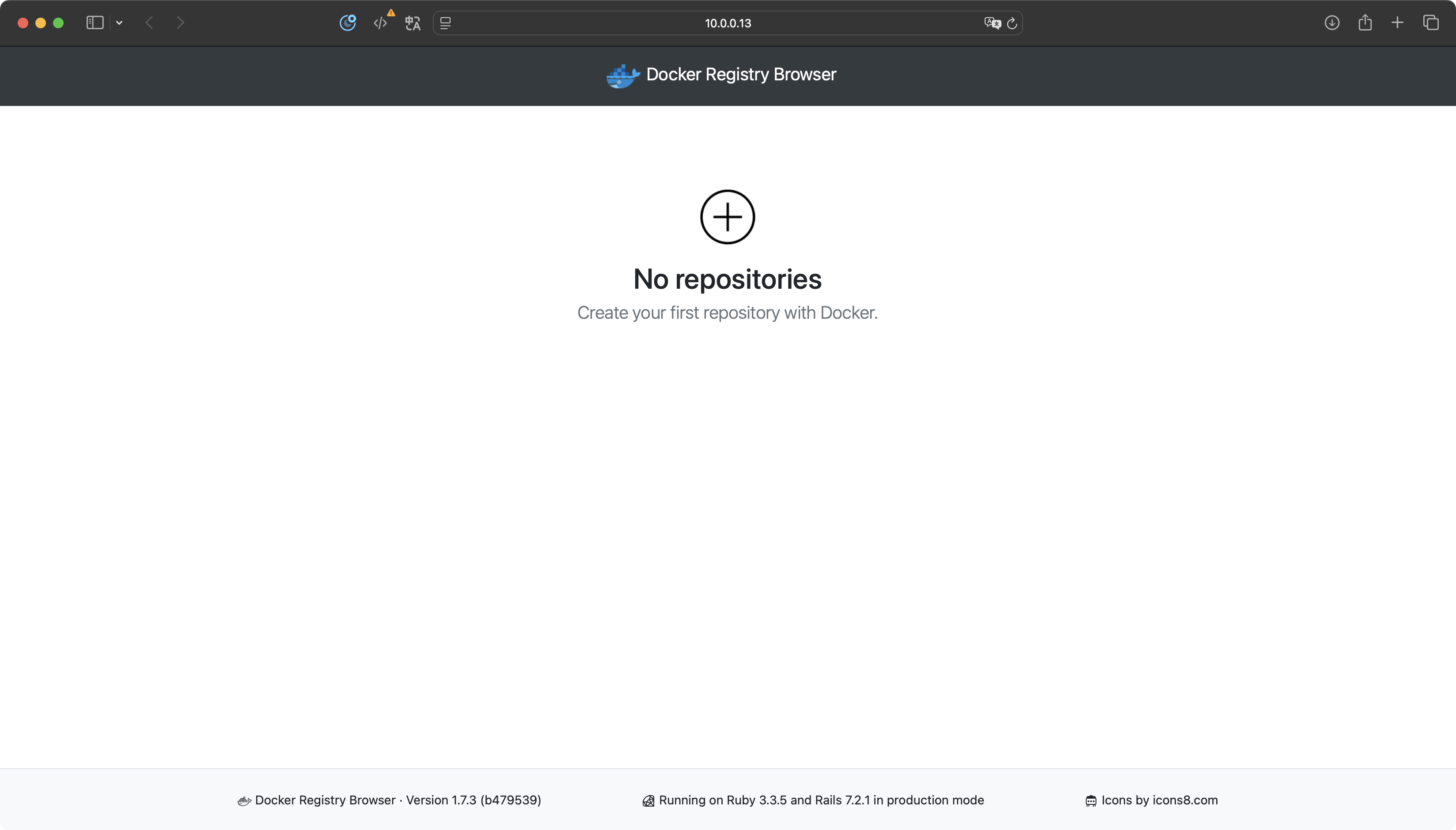
根据提示访问 50000 端口可以打开 DockerHub 的缓存 UI 界面,由于我们还没有拉取镜像所以现在是空的:
方法二:手动安装
虽让脚本安装比较简单,但是不够灵活,手动安装可以自己指定安装的服务类型、服务映射端口、镜像缓存目录等,如果想最大化自定义配置符合自己的需求最好还是手动安装。
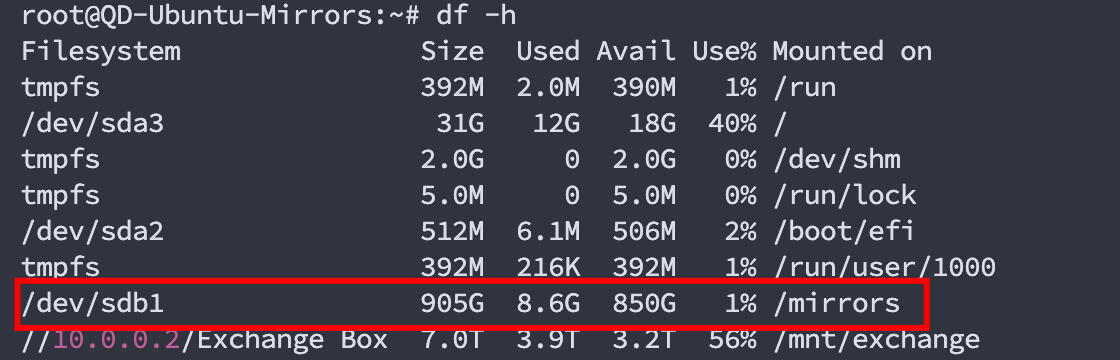
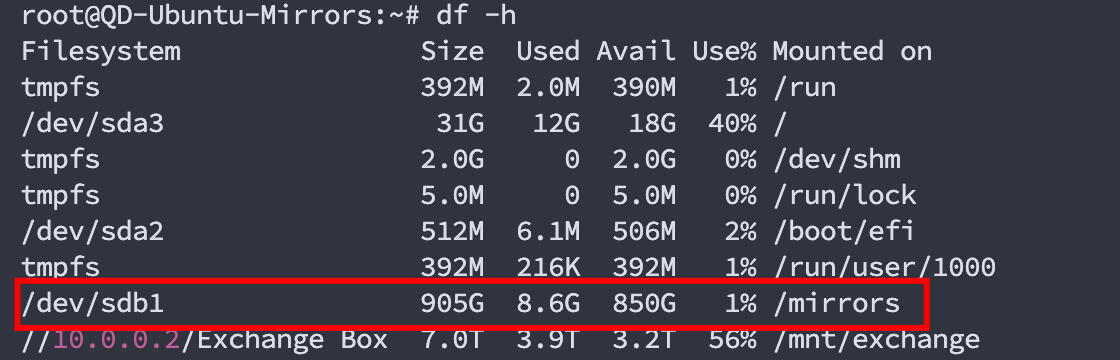
比如说为了给缓存镜像提供空间,我挂载了一块 1TB 的新磁盘到 /mirrors/registry-proxy 目录,而脚本安装只会安装到 /data/registry-proxy 目录无法更改,这样显示是不太方便的。
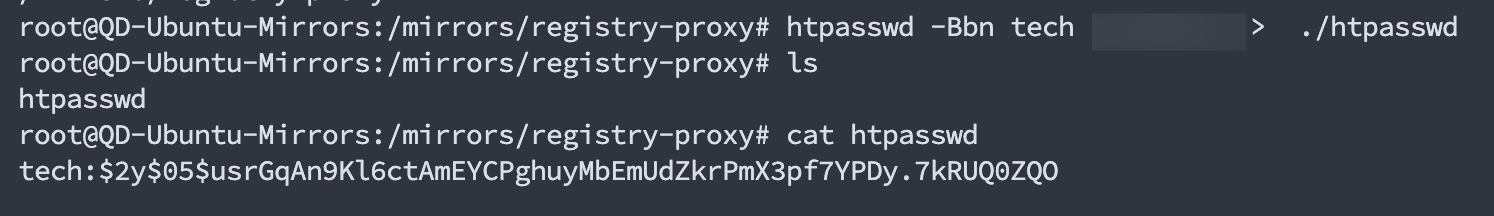
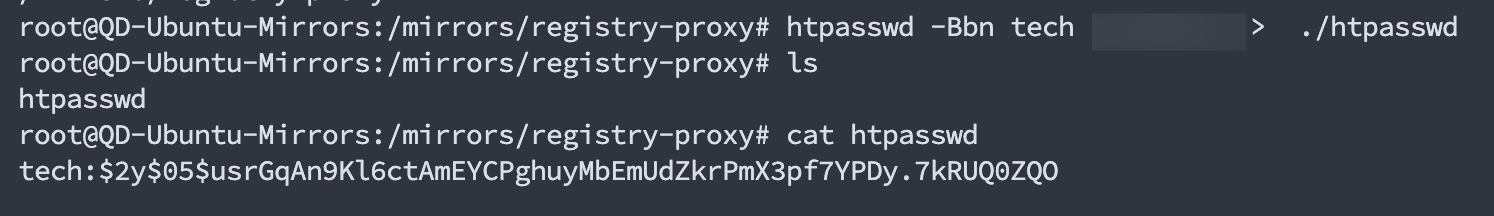
创建账号密码(可选)
设置密码认证后,我们在进行拉取镜像时就需要先 docker login登入到我们的自建的代理镜像仓库,然后才可以拉取镜像
1
2
| mkdir -p /mirrors/registry-proxy && cd $_
htpasswd -Bbn username password > ./htpasswd
|
编辑 docker-compose 文件
编辑我这里准备好的 docker-compose 文件,我默认运行项目所提供的全部镜像代理以及 UI,可以按需修改为自己需要的:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
| services:
dockerhub:
container_name: reg-docker-hub
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./docker-hub/data:/var/lib/registry
- ./docker-hub.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 51000:5000
networks:
- registry-net
ghcr:
container_name: reg-ghcr
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-ghcr/data:/var/lib/registry
- ./registry-ghcr.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 52000:5000
networks:
- registry-net
gcr:
container_name: reg-gcr
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-gcr/data:/var/lib/registry
- ./registry-gcr.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 53000:5000
networks:
- registry-net
k8sgcr:
container_name: reg-k8s-gcr
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-k8sgcr/data:/var/lib/registry
- ./registry-k8sgcr.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 54000:5000
networks:
- registry-net
k8s:
container_name: reg-k8s
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-k8s/data:/var/lib/registry
- ./registry-k8s.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 55000:5000
networks:
- registry-net
quay:
container_name: reg-quay
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-quay/data:/var/lib/registry
- ./registry-quay.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 56000:5000
networks:
- registry-net
mcr:
container_name: reg-mcr
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-mcr/data:/var/lib/registry
- ./registry-mcr.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 57000:5000
networks:
- registry-net
elastic:
container_name: reg-elastic
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-elastic/data:/var/lib/registry
- ./registry-elastic.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 58000:5000
networks:
- registry-net
nvcr:
container_name: reg-nvcr
image: dqzboy/registry:latest
restart: always
environment:
- OTEL_TRACES_EXPORTER=none
- http_proxy=http://10.0.0.13:7899
- https_proxy=http://10.0.0.13:7899
volumes:
- ./registry-nvcr/data:/var/lib/registry
- ./registry-nvcr.yml:/etc/distribution/config.yml
- ./htpasswd:/auth/htpasswd
ports:
- 59000:5000
networks:
- registry-net
registry-ui-docker:
container_name: registry-ui-docker
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-docker-hub:5000
- SECRET_KEY_BASE=0816a24b7ebd6b55069b72471ef6406b
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50010:8080
networks:
- registry-net
registry-ui-ghcr:
container_name: registry-ui-ghcr
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-ghcr:5000
- SECRET_KEY_BASE=faf1eaaacbed4136b6eb070c77e75e52
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50020:8080
networks:
- registry-net
registry-ui-gcr:
container_name: registry-ui-gcr
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-gcr:5000
- SECRET_KEY_BASE=d25b1dd04e29956c734c67761242feed
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50030:8080
networks:
- registry-net
registry-ui-k8sgcr:
container_name: registry-ui-k8sgcr
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-k8s-gcr:5000
- SECRET_KEY_BASE=0c1e18d1fb039a6bc4c6ac72c7037011
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50040:8080
networks:
- registry-net
registry-ui-k8s:
container_name: registry-ui-k8s
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-k8s:5000
- SECRET_KEY_BASE=eebf6d58eab1871981ab13bd9c39cdd5
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50050:8080
networks:
- registry-net
registry-ui-quay:
container_name: registry-ui-quay
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-quay:5000
- SECRET_KEY_BASE=70ff8298574a8e1612e163ba9129b271
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50060:8080
networks:
- registry-net
registry-ui-mcr:
container_name: registry-ui-mcr
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-mcr:5000
- SECRET_KEY_BASE=aca5275096a30c6b6335a24650728815
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50070:8080
networks:
- registry-net
registry-ui-elastic:
container_name: registry-ui-elastic
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-elastic:5000
- SECRET_KEY_BASE=a6124ad34099774cfd2e0a6473ae76a5
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50080:8080
networks:
- registry-net
registry-ui-nvcr:
container_name: registry-ui-nvcr
image: dqzboy/docker-registry-ui:latest
environment:
- DOCKER_REGISTRY_URL=http://reg-nvcr:5000
- SECRET_KEY_BASE=c590711a4abf62e62a100c81fe0db679
- ENABLE_DELETE_IMAGES=true
- NO_SSL_VERIFICATION=false
restart: always
ports:
- 50090:8080
networks:
- registry-net
networks:
registry-net:
driver: bridge
|
编辑 config.yml 配置文件
这里的配置文件需要和上一步 docker-compose.yaml 文件中映射的一致,每一个镜像缓存服务都需要对应一个 config.yml 配置文件。篇幅关系这里只给出 DockerHub 和 ghcr 的配置文件,每个配置文件需要修改的地方基本上只有最后一个上游镜像地址块:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
| version: 0.1
log:
fields:
service: registry
storage:
filesystem:
rootdirectory: /var/lib/registry
delete:
enabled: true
cache:
blobdescriptor: inmemory
blobdescriptorsize: 10000
maintenance:
uploadpurging:
enabled: true
age: 168h
interval: 24h
dryrun: false
readonly:
enabled: false
http:
addr: :5000
headers:
X-Content-Type-Options: [nosniff]
Access-Control-Allow-Origin: ['*']
Access-Control-Allow-Methods: ['HEAD', 'GET', 'OPTIONS', 'DELETE']
Access-Control-Allow-Headers: ['Authorization', 'Accept', 'Cache-Control']
Access-Control-Max-Age: [1728000]
Access-Control-Allow-Credentials: [true]
Access-Control-Expose-Headers: ['Docker-Content-Digest']
auth:
htpasswd:
realm: basic-realm
path: /auth/htpasswd
health:
storagedriver:
enabled: true
interval: 10s
threshold: 3
proxy:
remoteurl: https://registry-1.docker.io
username:
password:
ttl: 168h
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
| version: 0.1
log:
fields:
service: registry
storage:
filesystem:
rootdirectory: /var/lib/registry
delete:
enabled: true
cache:
blobdescriptor: inmemory
blobdescriptorsize: 10000
maintenance:
uploadpurging:
enabled: true
age: 168h
interval: 24h
dryrun: false
readonly:
enabled: false
http:
addr: :5000
headers:
X-Content-Type-Options: [nosniff]
Access-Control-Allow-Origin: ['*']
Access-Control-Allow-Methods: ['HEAD', 'GET', 'OPTIONS', 'DELETE']
Access-Control-Allow-Headers: ['Authorization', 'Accept', 'Cache-Control']
Access-Control-Max-Age: [1728000]
Access-Control-Allow-Credentials: [true]
Access-Control-Expose-Headers: ['Docker-Content-Digest']
auth:
htpasswd:
realm: basic-realm
path: /auth/htpasswd
health:
storagedriver:
enabled: true
interval: 10s
threshold: 3
proxy:
remoteurl: https://ghcr.io
username:
password:
ttl: 168h
|
全部配置好后的目录结构应该是这样的:

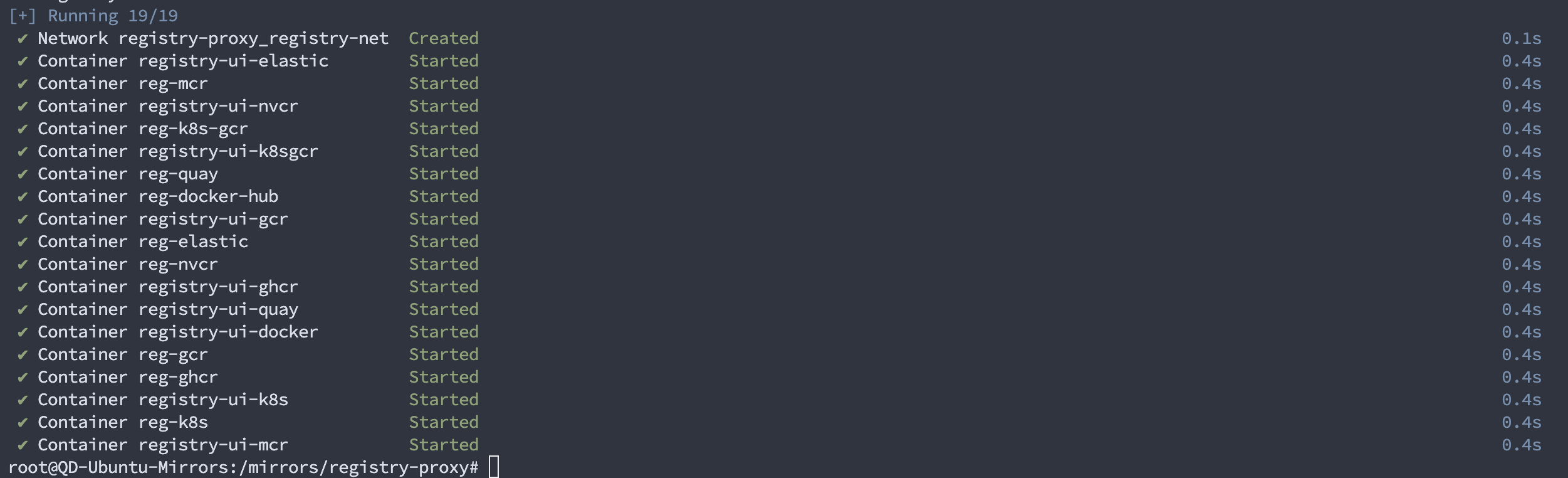
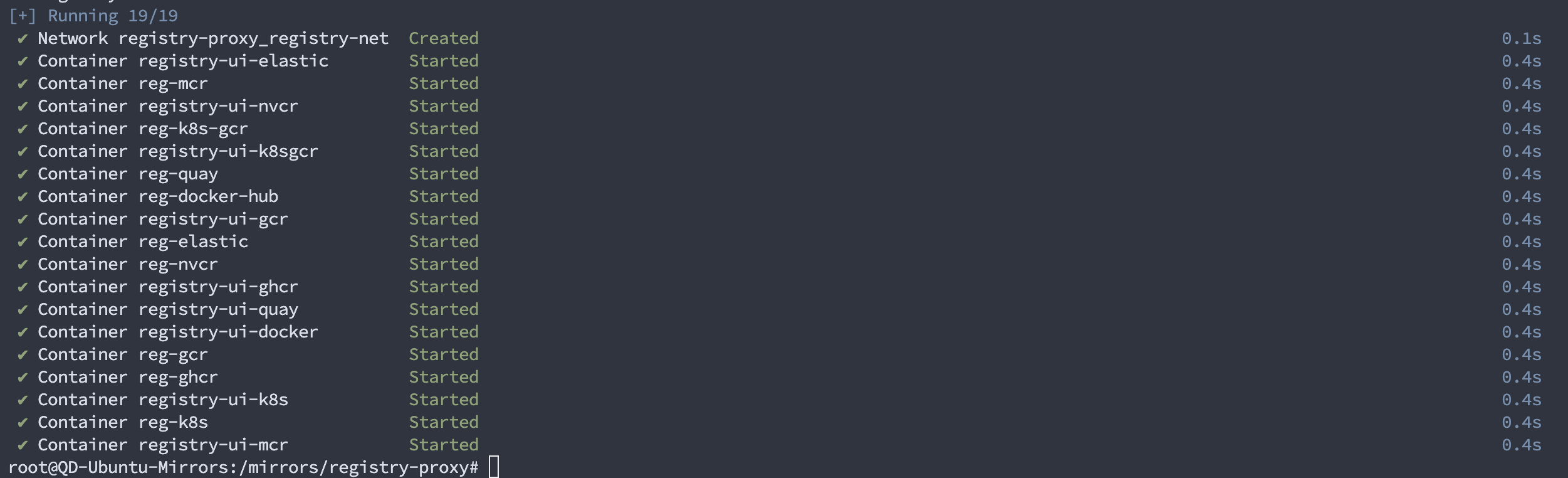
启动服务

配置 Nginx 反向代理
安装 nginx:
配置 nginx:
1
2
| cd /etc/nginx/conf.d/
vim registry-proxy.conf
|
这里给出一份 nginx 示例配置文件:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
401
402
403
404
405
406
407
408
409
410
411
412
413
414
415
416
417
418
419
420
421
422
423
424
425
426
427
428
429
430
431
432
433
434
435
436
437
438
439
440
441
442
443
444
445
446
447
448
449
450
451
452
453
454
455
456
457
458
459
460
461
462
463
464
465
466
467
468
469
470
471
472
473
474
475
476
477
478
479
480
481
482
483
484
485
486
487
488
489
490
491
492
493
494
495
496
497
498
499
500
501
502
503
504
505
506
507
508
509
510
511
512
513
514
515
516
517
518
519
520
521
522
523
524
525
526
527
528
529
530
531
532
533
534
535
536
537
538
539
540
541
542
543
544
545
546
547
548
549
550
551
552
553
554
555
556
557
558
559
560
561
562
563
564
565
566
567
568
|
server {
listen 80;
listen 443 ssl;
server_name docker-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50010;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name ghcr-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50020;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name gcr-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50030;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name k8sgcr-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50040;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name k8s-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50050;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name quay-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50060;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name mcr-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50070;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name elastic-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50080;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name nvcr-ui.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:50090;
proxy_set_header Host $host;
proxy_set_header Origin $scheme://$host;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Ssl on;
proxy_set_header X-Forwarded-Port $server_port;
proxy_set_header X-Forwarded-Host $host;
}
}
server {
listen 80;
listen 443 ssl;
server_name docker.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:51000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name ghcr.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:52000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name gcr.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:53000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name k8sgcr.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:54000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name k8s.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:55000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name quay.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:56000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name mcr.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:57000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name elastic.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:58000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
server {
listen 80;
listen 443 ssl;
server_name nvcr.inc.tddt.io;
ssl_certificate /etc/nginx/certs/inc.tddt.io.crt;
ssl_certificate_key /etc/nginx/certs/inc.tddt.io.key;
ssl_session_timeout 1d;
ssl_session_cache shared:SSL:50m;
ssl_session_tickets off;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers ECDHE-RSA-AES128-GCM-SHA256:HIGH:!aNULL:!MD5:!RC4:!DHE;
ssl_prefer_server_ciphers on;
ssl_buffer_size 8k;
proxy_connect_timeout 600;
proxy_send_timeout 600;
proxy_read_timeout 600;
send_timeout 600;
location / {
proxy_pass http://localhost:59000;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Nginx-Proxy true;
proxy_buffering off;
proxy_redirect off;
}
}
|
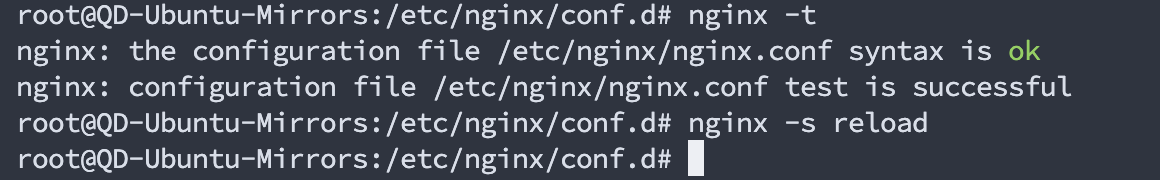
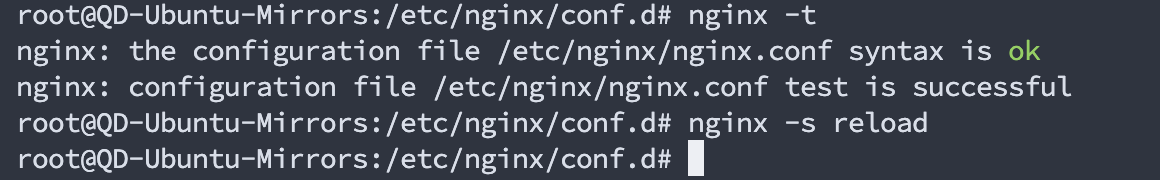
重载 nginx:
1
2
| nginx -t
nginx -s reload
|
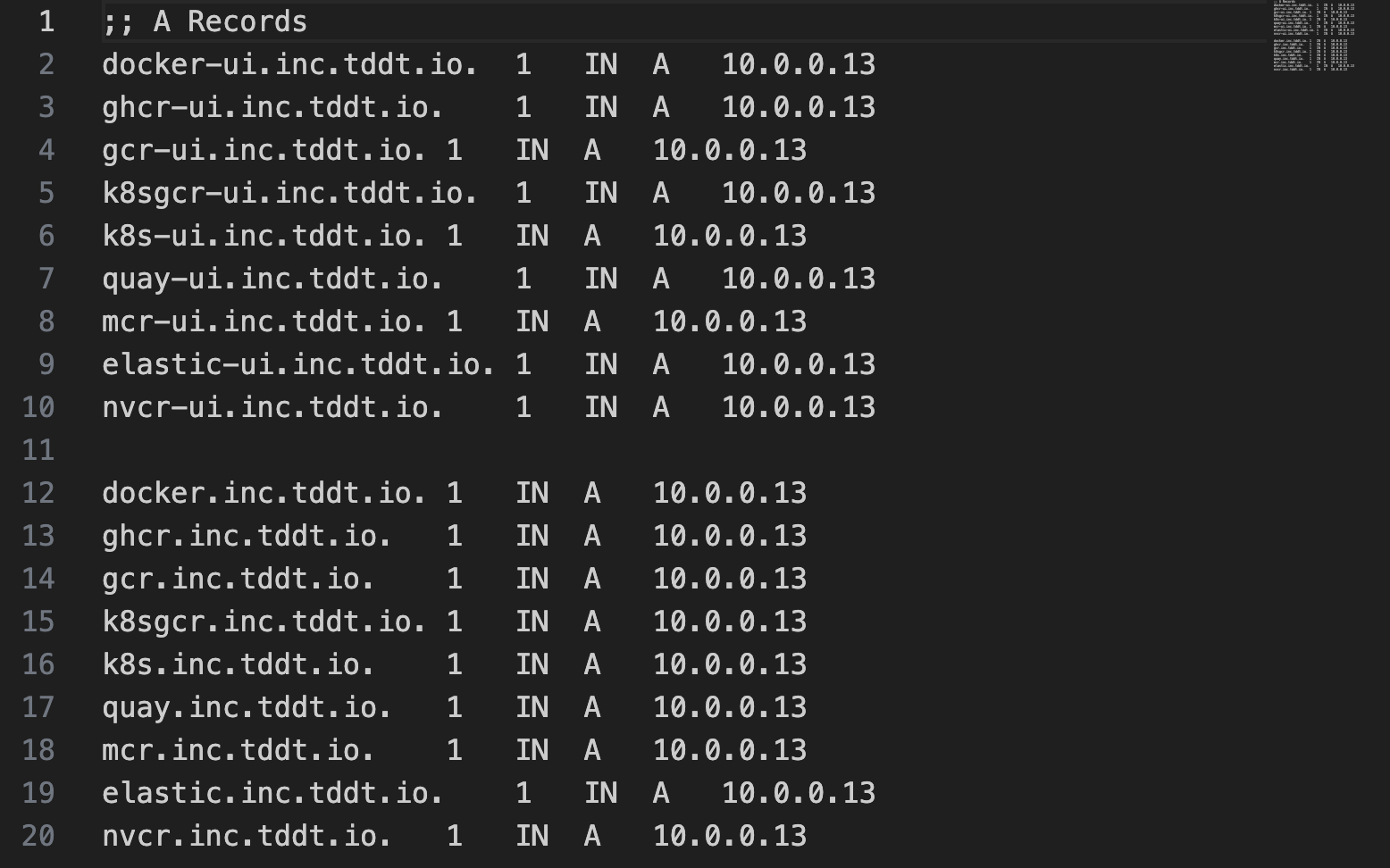
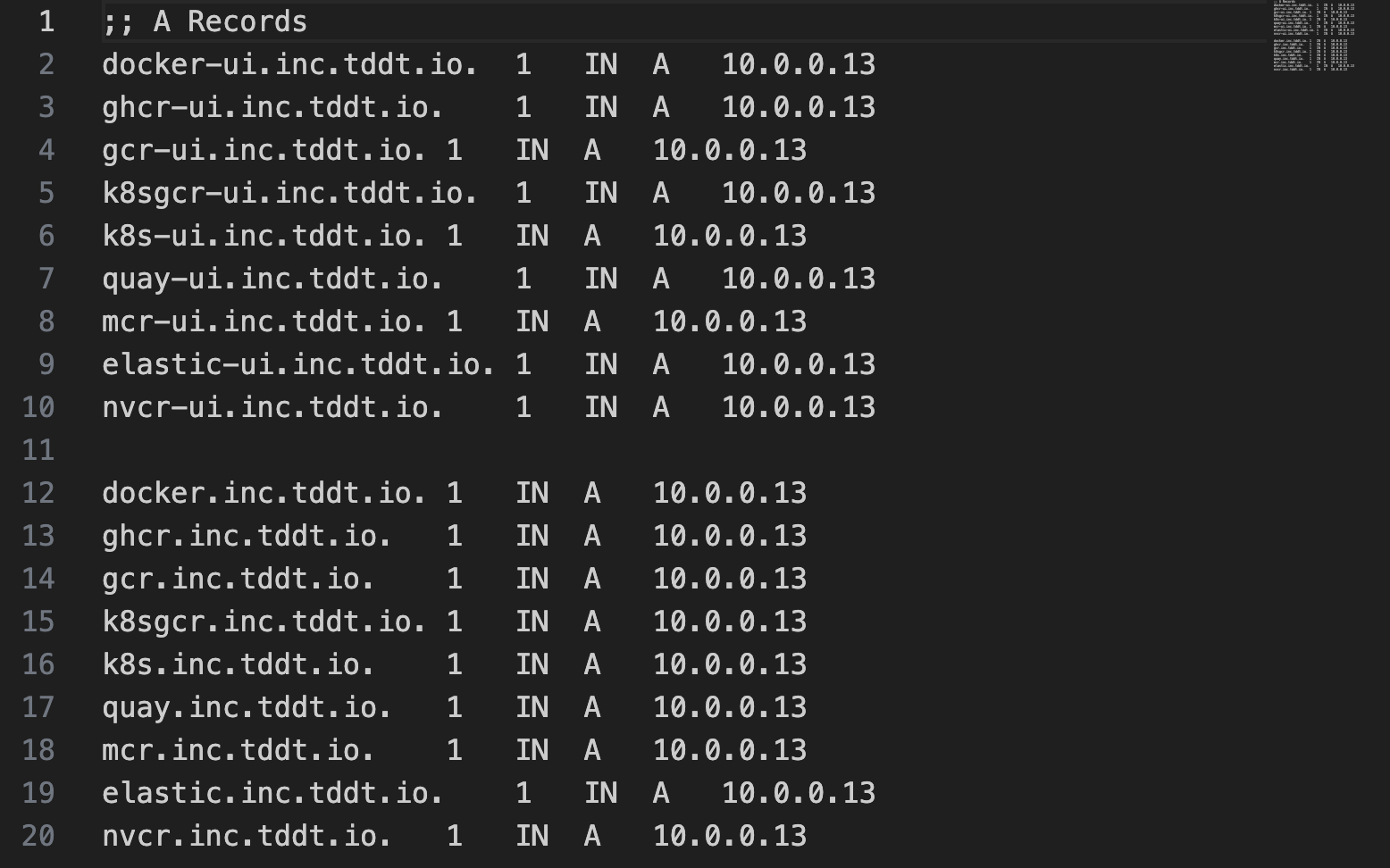
配置域名解析
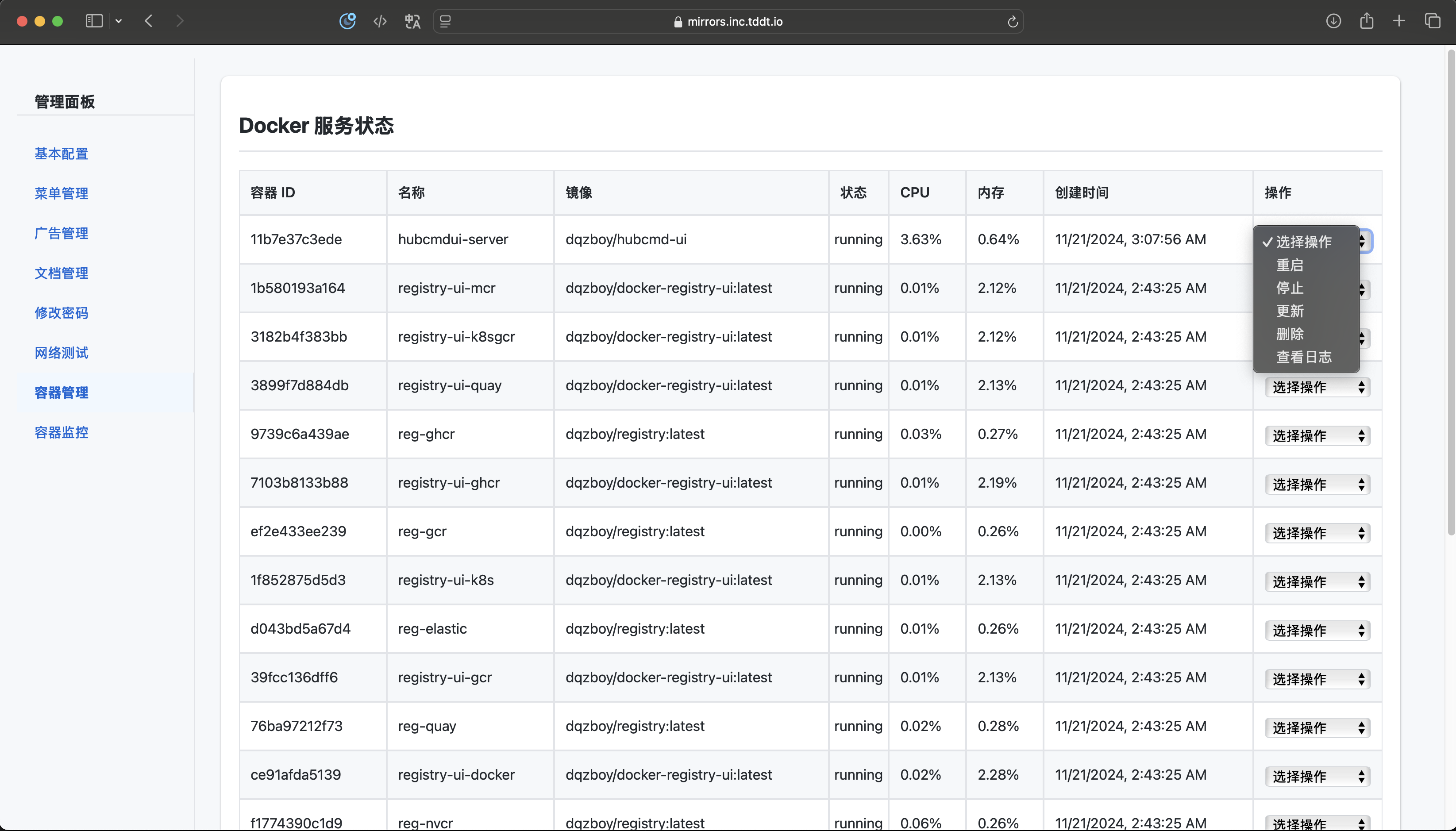
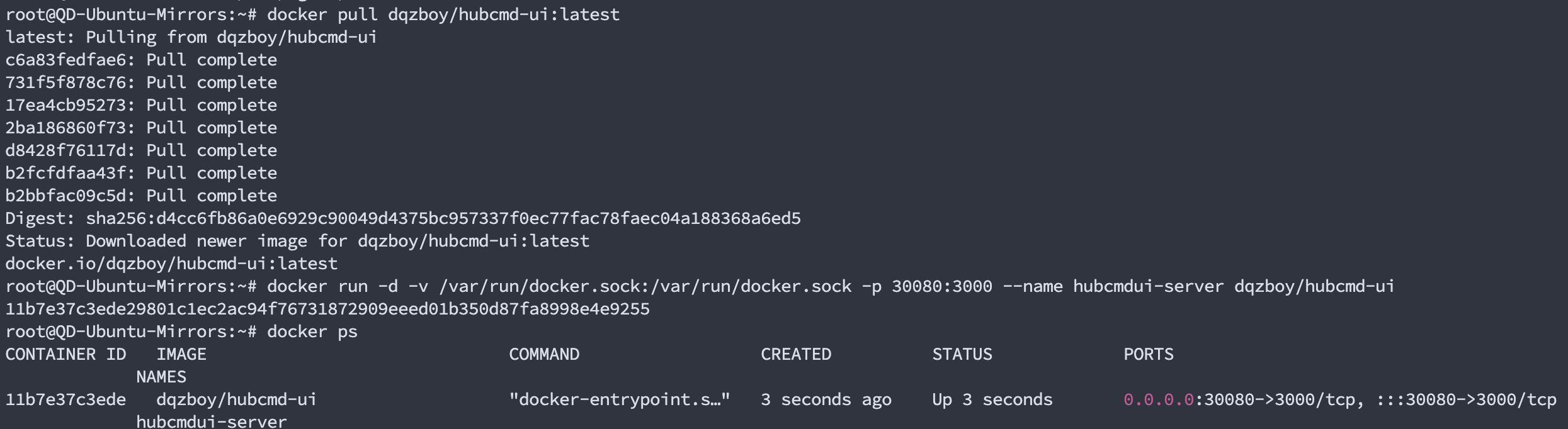
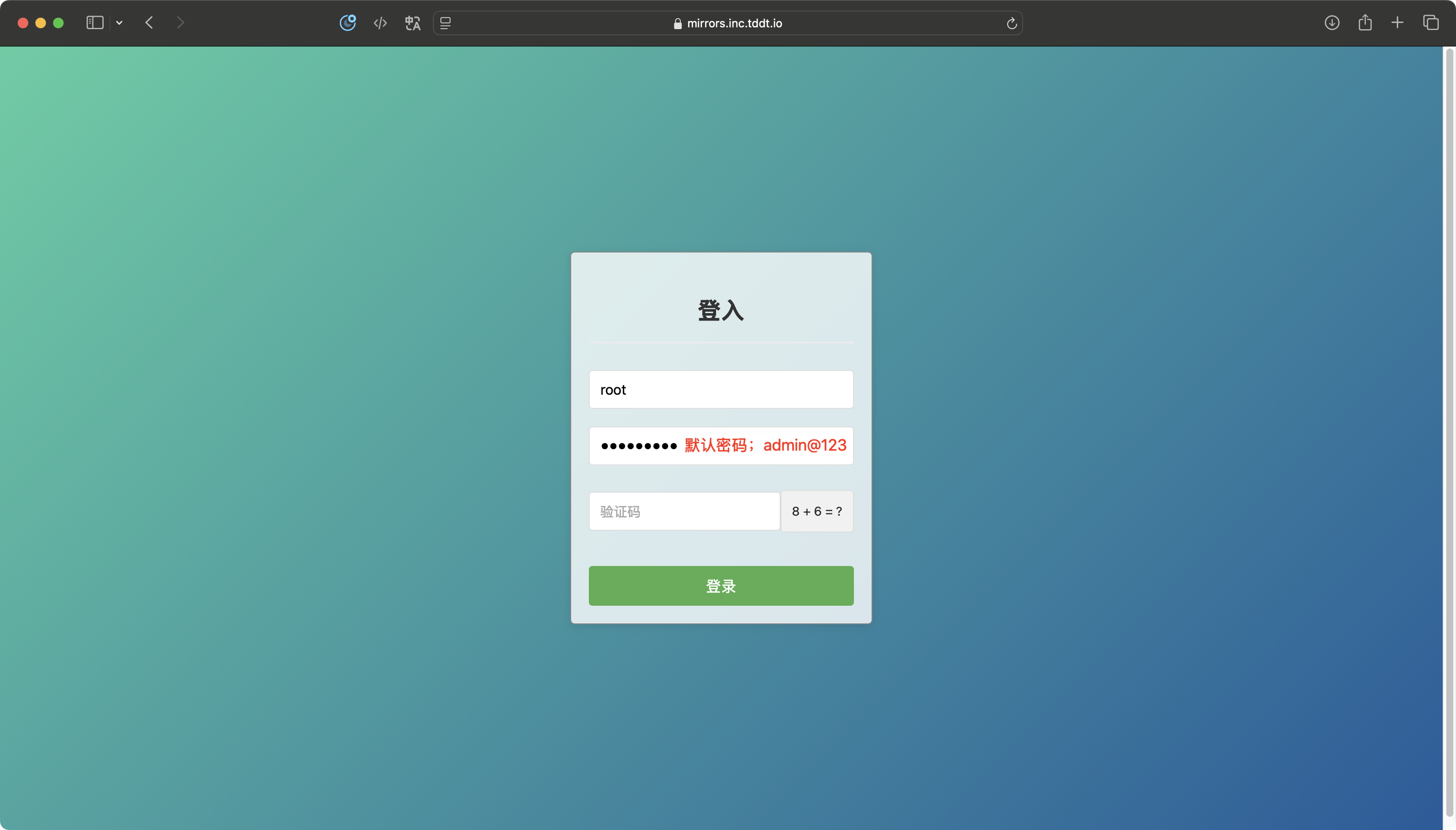
部署 CMDUI (可选)
到这一步其实已经可以正常使用了,但是为了方便管理可以再部署一个管理面板。
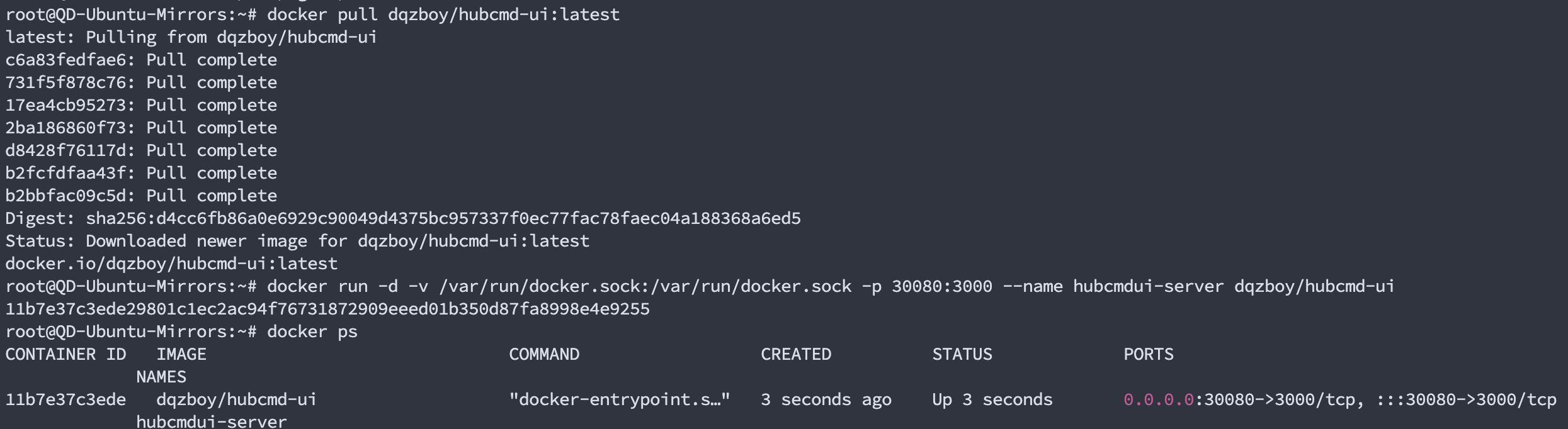
直接拉取 CMDUI 镜像运行:
1
2
| docker pull dqzboy/hubcmd-ui:latest
docker run -d -v /var/run/docker.sock:/var/run/docker.sock -p 30080:3000 --name hubcmdui-server dqzboy/hubcmd-ui
|
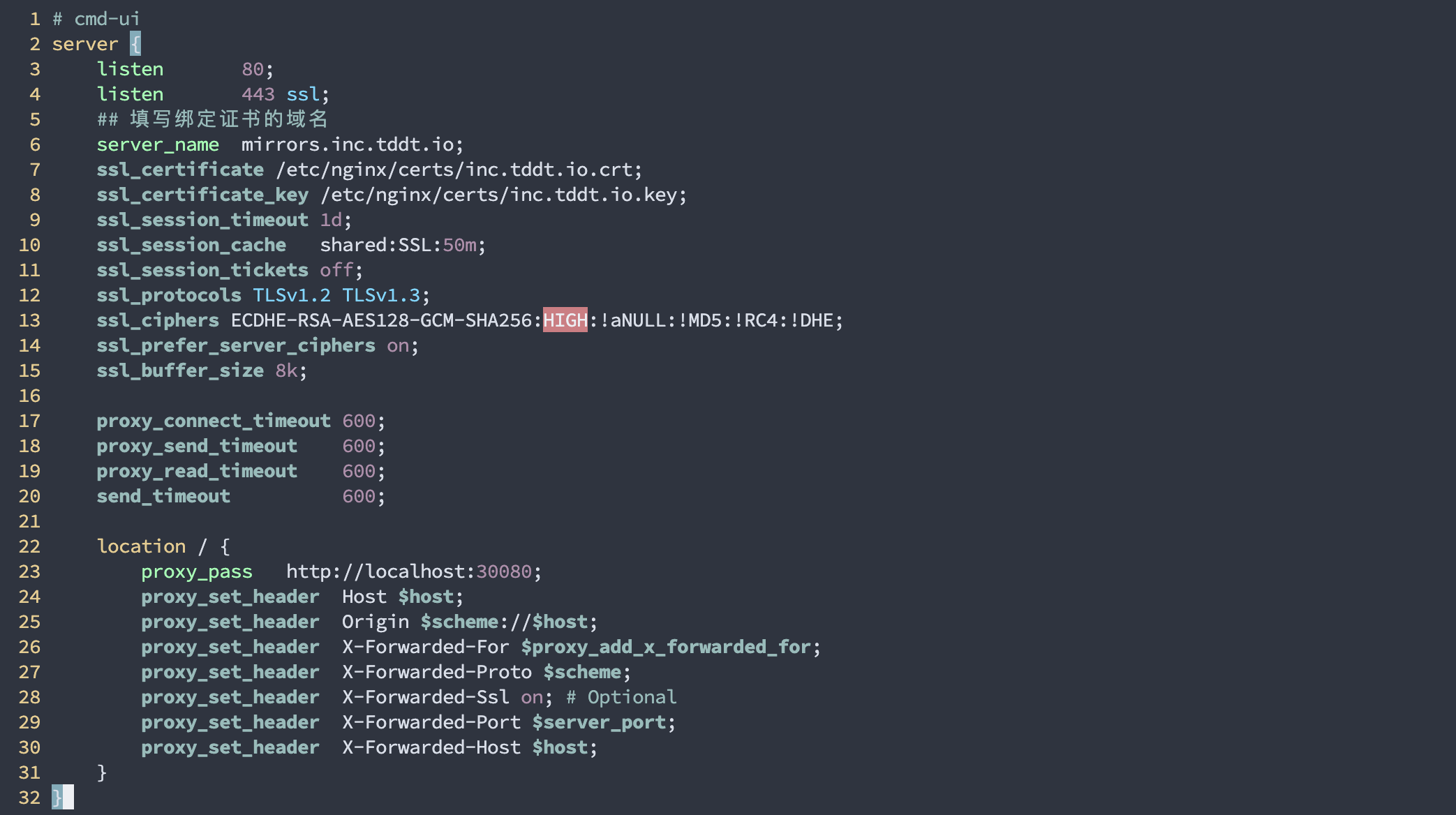
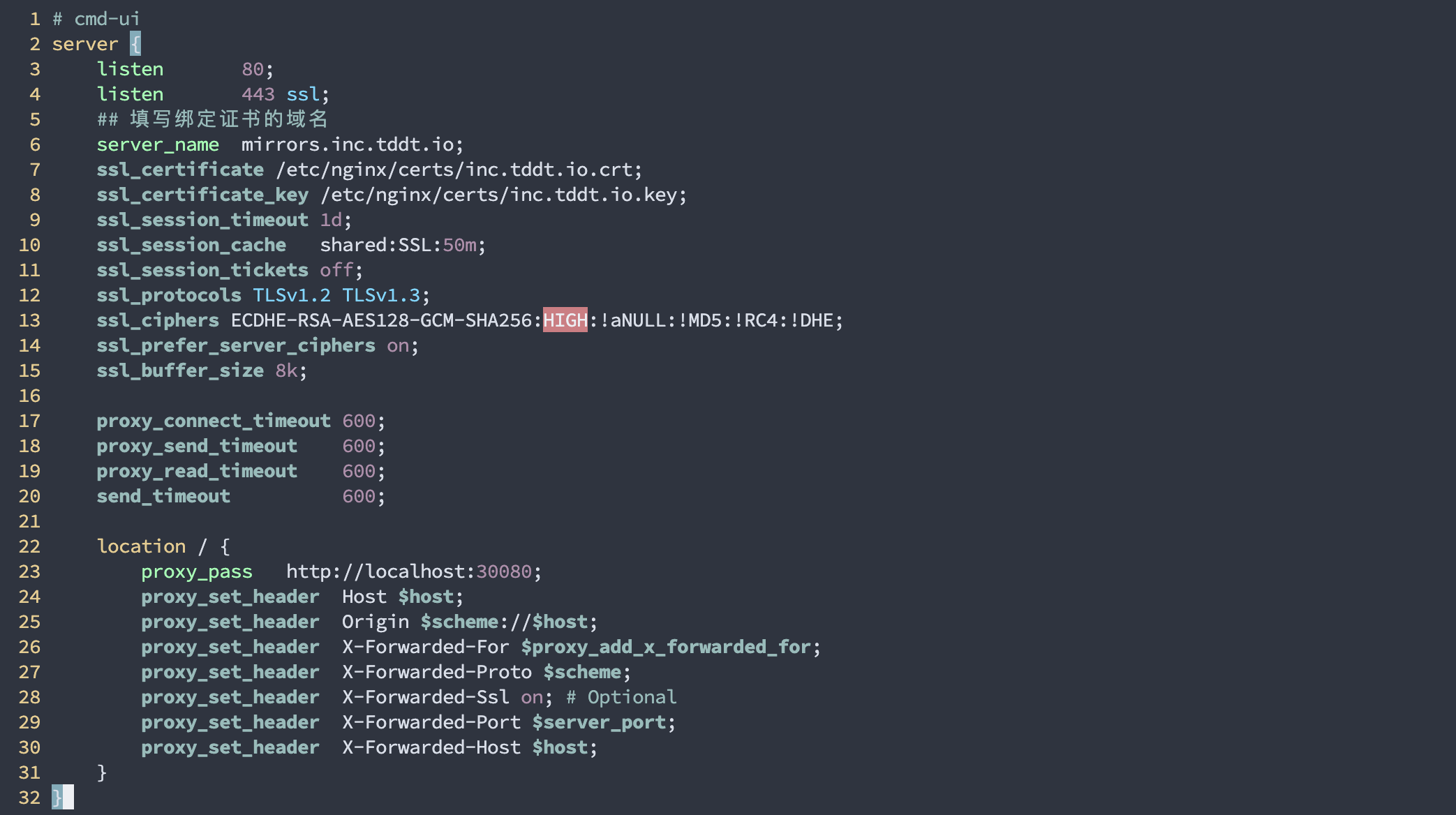
再补充一个 cmd-ui 的反代配置:
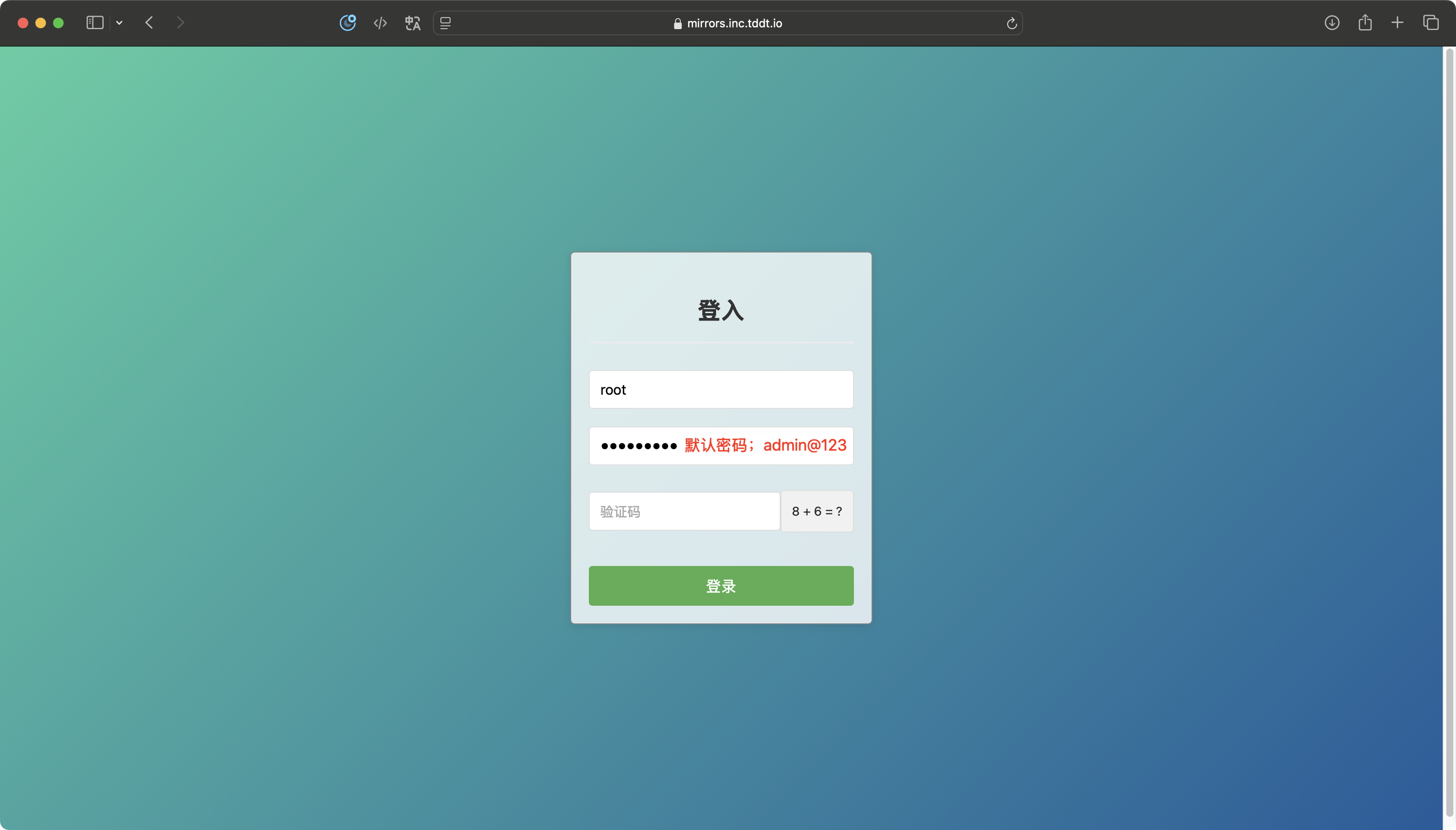
访问测试

使用镜像仓库代理
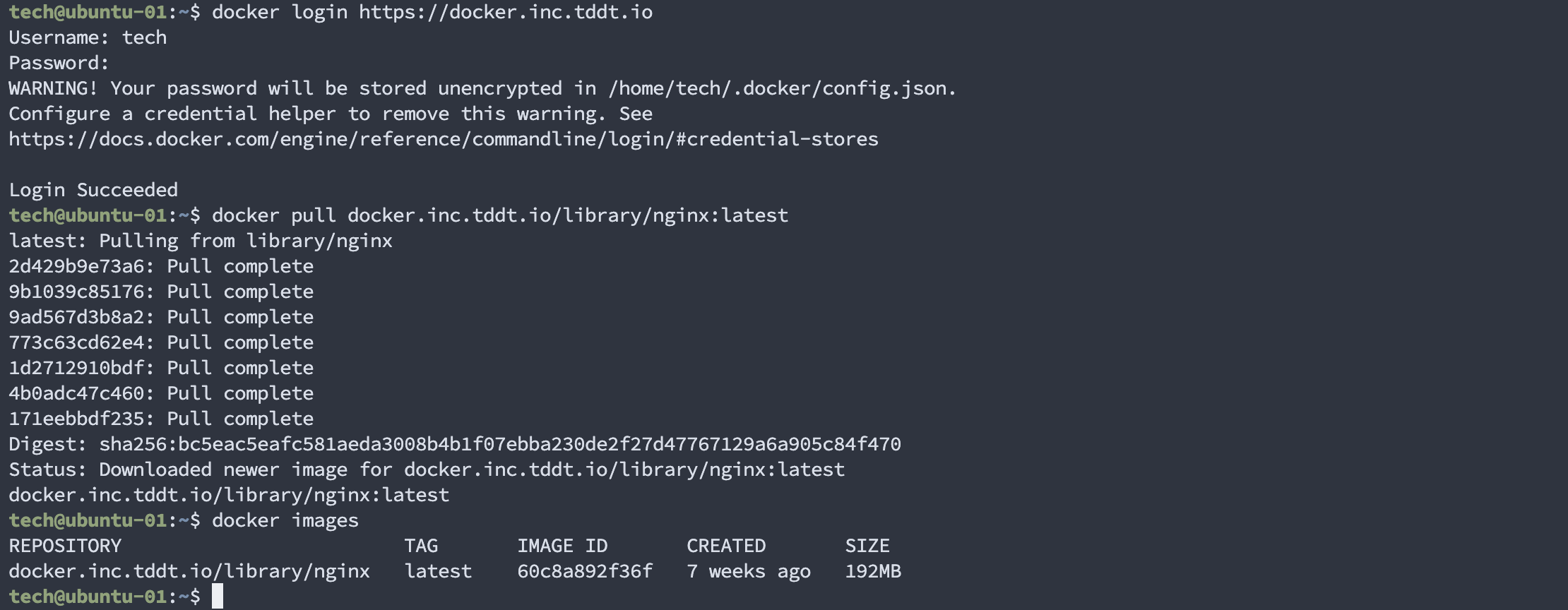
方法一:使用自建地址替换原地址
1
2
| docker login https://docker.inc.tddt.io
docker pull docker.inc.tddt.io/library/nginx:latest
|
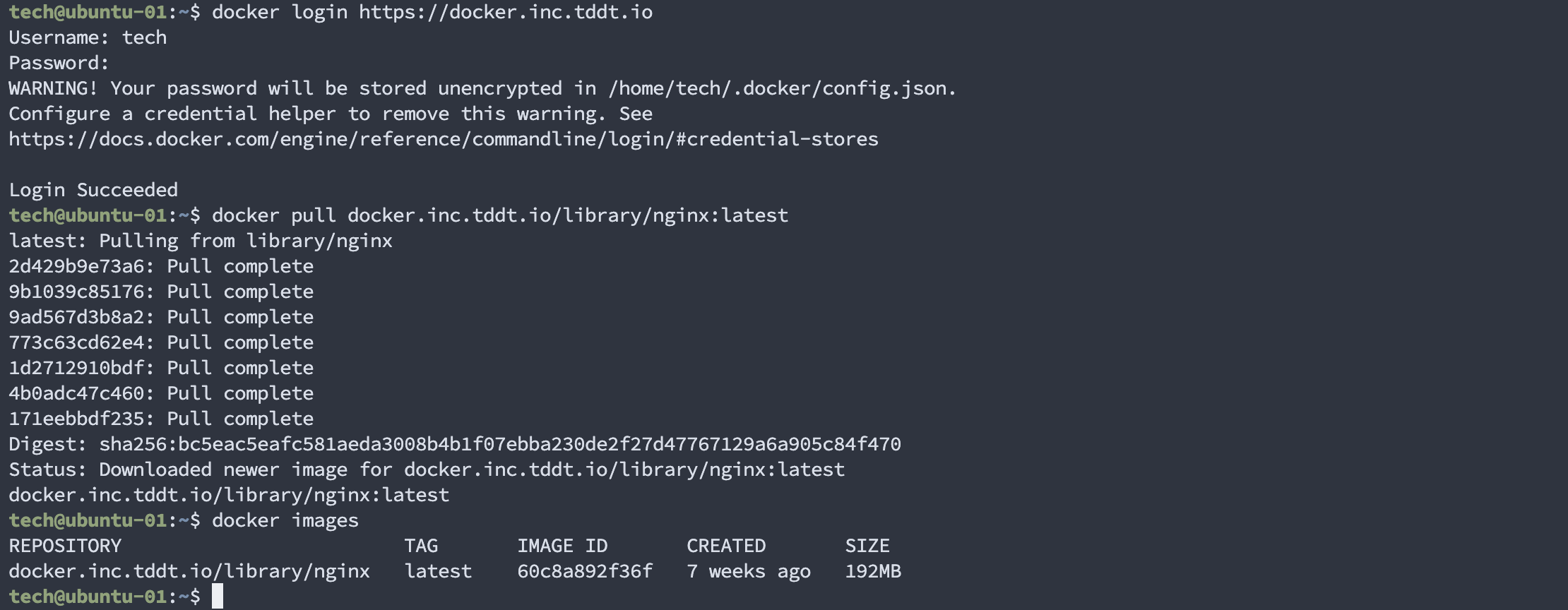
此时访问 UI 页面就可以看到上面我们下载的镜像已经被缓存了:

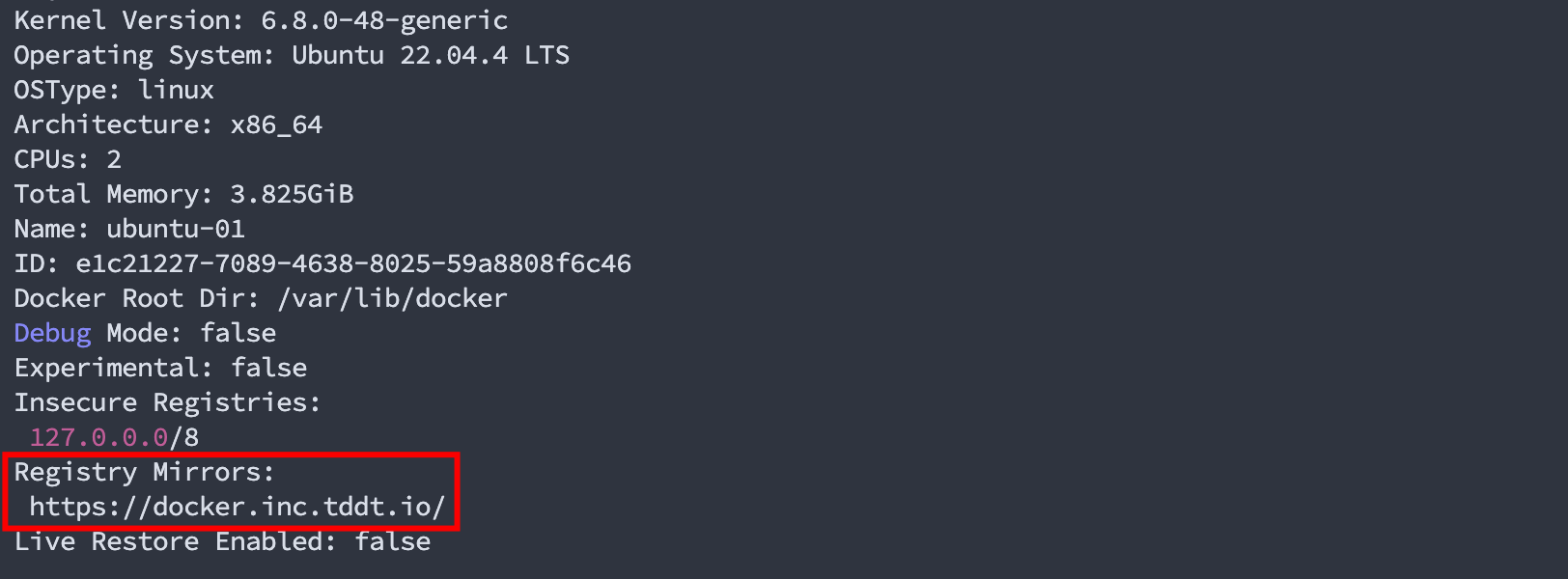
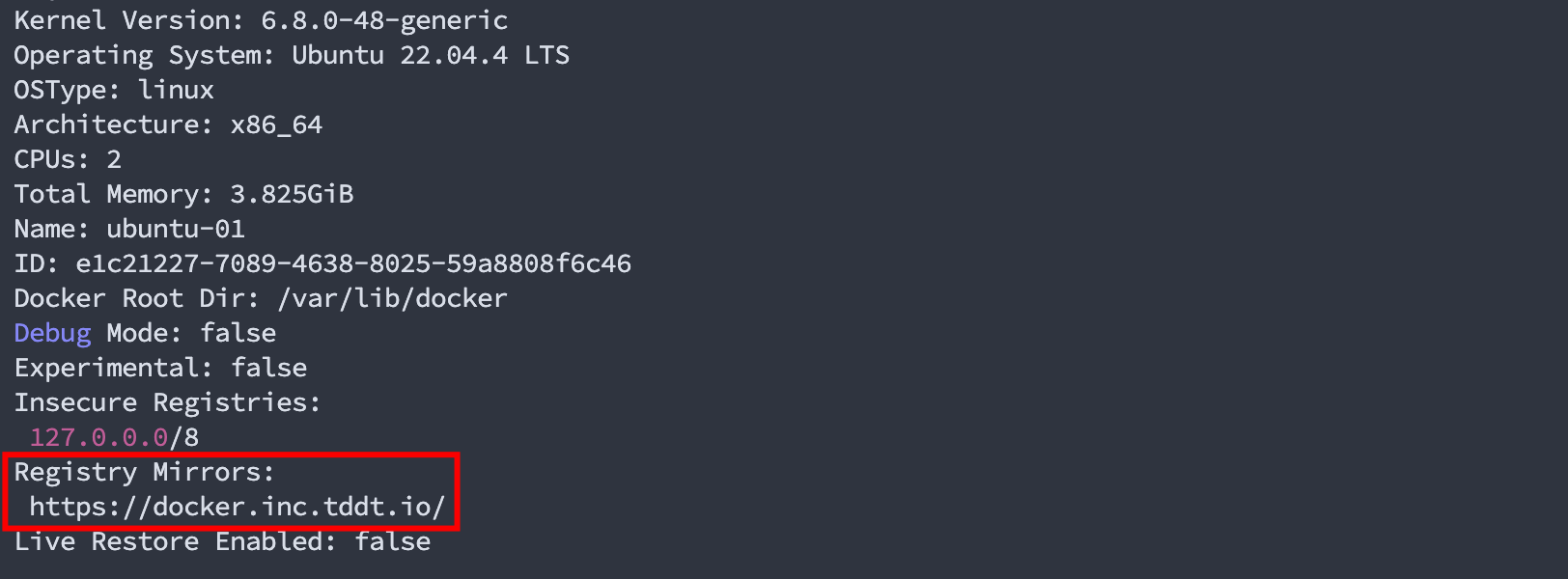
方法二:修改 docker 配置
1
2
3
4
5
6
7
8
9
10
11
| vim /etc/docker/daemon.json
{
"registry-mirrors": ["https://docker.inc.tddt.io"],
"log-opts": {
"max-size": "100m",
"max-file": "5"
}
}
systemctl restart docker
|

查看 docker 配置,如何能看到我们添加的镜像代理地址就可以了:
参考